Editor’s note: This report was authored by Alexa Feminella and James Xiang
Key Points
Extortion group “ShinyHunters” appears to be shifting to branded subdomain impersonation (single sign-on [SSO]/Okta-themed) paired with phone-guided, adversary-in-the middle (AiTM) phishing and mobile-first lure engagement. It’s also scaling its reach through outsourced spam/pressure services and recruitment of additional voice operators.
In addition, the group is likely reusing previously exposed software-as-a-service (SaaS) records to build believable pretexts and identify the “next best” person to socially engineer, creating a repeatable access loop.
The result is rapid identity-to-SaaS compromise: A single valid SSO session or help-desk reset can enable broad access to emails, files, HR, and customer relationship management (CRM) data—without deploying malware.
Prioritize phishing-resistant MFA, hardened reset and MFA re-enrollment workflows, identity and session telemetry with rapid containment, and improved visibility for mobile-driven authentication.
The financially motivated threat group “ShinyHunters” appears to be shifting to subdomain impersonation to drive initial access. It’s highly likely that this is a deliberate move away from using newly registered lookalike domains to an approach that can slip past traditional “new domain” controls.
Two parallel developments further shorten the group’s time-to-impact: lures designed with mobile users in mind (reducing visibility in enterprise network monitoring and web filtering) and paid criminal outsourcing (to scale the group’s email-, SMS-, and phone-based outreach).
Targets from earlier campaigns (including the high-profile Salesforce campaign) also continue to appear, suggesting ShinyHunters is likely reusing previously stolen customer relationship management (CRM) and enterprise resource planning (ERP) datasets to drive repeat and follow-on social engineering.
Subdomain impersonation paired with social engineering speeds up software-as-a-service (SaaS) compromise through session theft and help-desk–driven MFA resets. With a valid single sign-on (SSO) session, attackers can quickly pivot across SaaS applications. Because branding sits in the subdomain, domain controls may miss these lures. Easy to replicate, this tradecraft demands phishing-resistant MFA, identity telemetry, and rapid session containment beyond domain monitoring.
In this spotlight, we:
Break down ShinyHunters’ subdomain patterns, phishing-kit usage, and mobile-driven lure delivery.
Explain how recycled CRM and ERP data creates a repeatable social engineering loop across SaaS.
Detail how ShinyHunters is scaling pressure tactics and provide actionable guidance to detect, contain, and anticipate these intrusion paths.
Hiding Brand Lures in Subdomains
ShinyHunters is making brand impersonation harder to catch with traditional domain-based monitoring by shifting the “brand signal” out of the domain name that defenders typically watch (the registered domain) and into the subdomain.
In previous activity, the group typically registered lookalike support domains to host phishing pages or help-desk–themed lures, placing the target organization’s name directly in the domain (e.g., ticket-<organization>[.]com or <organization>-support[.]com). Now, ShinyHunters is using generic, non-brand domains and putting the organization branding in the subdomain (e.g., <organization>.sso-verify[.]com).
This reduces the effectiveness of traditional controls that focus on newly registered domains, typo-squats, and suspicious-looking domain names. To help security teams defend against this approach, ReliaQuest is actively tracking these domains as they appear and monitoring for related activity.
In practice, the registered domain is often SSO- or login-themed and otherwise unremarkable, helping the infrastructure blend in. Domain monitoring still matters, but it’s less likely to surface the lure early when the “brand” no longer appears where many detections prioritize.
Examples:
<organization>.sso[.]guide
<organization>.okta[.]guide
<organization>.acess-terms[.]com
Beyond URL structure, we’ve also seen clustered targeting: Certain domain families are disproportionately tied to specific industry verticals and, in some cases, regions.
For example, okta[.]guide and sso[.]guide skew toward health care and pharmaceutical brands, while access-terms[.]com more frequently targets UK organizations. This points to a scalable model where threat actors rapidly generate organization-branded subdomains with vertical-specific pretexts—while reusing the same underlying infrastructure.
Echoes of Scattered Spider but Links to ShinyHunters
We attribute these domains with high confidence to ShinyHunters based on multiple corroborating factors across incidents: hands-on-keyboard use of the subdomains during organization-facing vishing, end-to-end intrusion sequences consistent with public reporting, and clustered registration patterns tied to shared registrar and nameserver infrastructure.
The lure themes also align with earlier ShinyHunters activity, mimicking common identity workflows like Okta setup, SSO portals, and “access” prompts, but the infrastructure design is different. By keeping the registered domain generic and rotating subdomains by target, ShinyHunters can retarget quickly. These pages may also use valid Transport Layer Security (TLS), i.e., a padlock/HTTPS, and polished language that closely mirrors legitimate SSO workflows, increasing end-user trust despite attacker control.
The subdomain impersonation patterns also resemble tactics we’ve seen from the cybercriminal collective “Scattered Spider.” While the level of direct coordination between the groups is unclear, the overlap (and our prior reporting on commonalities between the groups) suggests ShinyHunters is likely adopting tradecraft that’s already proven effective in adjacent social-engineering campaigns.
Mobile-First, Phone-Guided AiTM Accelerates Session Theft
As in previous ShinyHunters activity, we observed behavior consistent with adversary-in-the-middle (AitM) phishing kits—tools that proxy the login flow to capture credentials, MFA challenges, and, most importantly, authenticated sessions in real time. In this campaign, subdomain impersonation appears purpose-built for live, phone-guided delivery and mobile-first engagement.
A typical workflow is straightforward:
The operator calls the end user using a help-desk or support pretext.
The user is directed to an organization-branded impersonation subdomain.
The operator guides the user through authentication and MFA on a mobile device.
The user completes an SSO login flow that is proxied by the attacker.
The attacker uses the captured authenticated session to access and exfiltrate SaaS data.
Users may be routed through staged pages (for example, anti-bot verification steps followed by SSO and MFA prompts and a confirmation page). In sandboxing, we observed anti-bot gating consistent with Cloudflare Turnstile (see Figure 1), which can deter automated analysis and is commonly associated with phishing-kit infrastructure.
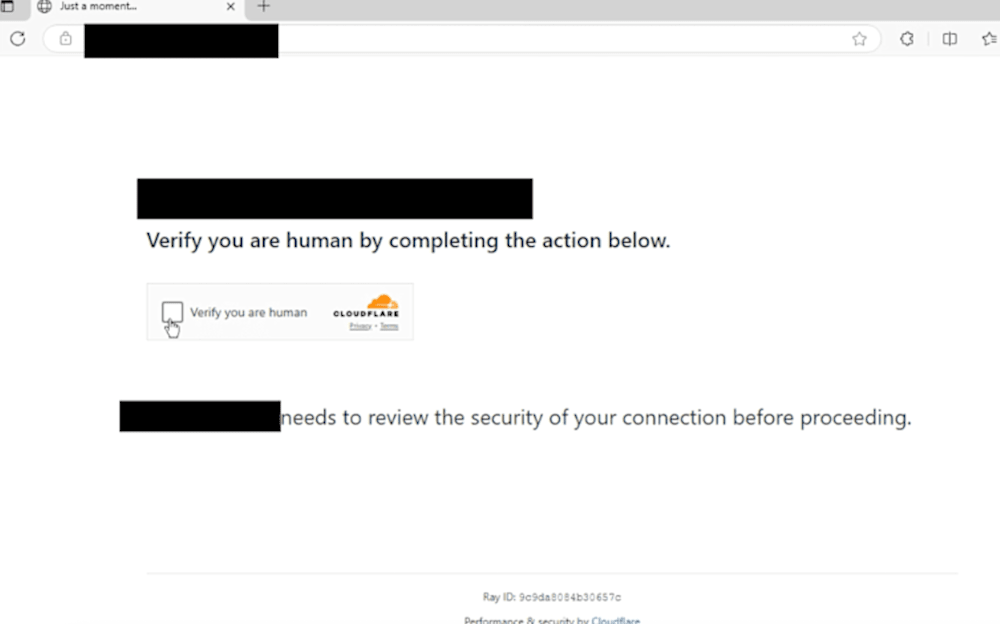
Figure 1: Sandbox of subdomain shows Cloudflare Turnstile
In incident data and related lure telemetry, targets frequently opened these URLs from mobile user agents (and in several cases, outside typical corporate egress), which can reduce visibility in corporate DNS filtering, proxy telemetry, and managed endpoint controls. The effect is compounded when the registered domain looks generic and the “brand” appears only in the subdomain.
Together, subdomain impersonation plus mobile/voice-guided AiTM weakens controls focused on newly registered domains and obvious lookalikes. Defenders should complement domain monitoring with URL-level visibility and identity-driven detection (suspicious sign-in patterns and session anomalies) and harden help-desk verification and MFA re-enrollment workflows.
Yesterday’s SaaS Breach, Today’s Target List
ShinyHunters isn’t just stealing data from SaaS systems of record. The group is likely reusing previously exposed datasets from CRM, ERP, HR, and productivity platforms to power follow-on social engineering. Our investigations show this reuse is consistent: Current outreach repeatedly aligns with individuals from prior SaaS datasets (including CRM-focused campaigns). In practice, this means that attackers can use these records to quickly identify the “next best” person to pressure—someone positioned to approve access, reset credentials, or re-enroll MFA.
These datasets make pretexts more credible because they include employee names, roles, reporting lines, user identifiers, and employee context. The result is that older breach data remains operationally dangerous long after remediation if employee, contact, and customer information isn’t treated as long-lived sensitive material. It enables vishing at scale, supports repeated access attempts, expands SaaS reach, and increases extortion leverage.
ShinyHunters pairs this targeting advantage with user-facing infrastructure that looks routine. Even as organizations harden help desks, operators can bypass that friction by calling end users directly and steering them to SSO-themed lures. In SaaS-heavy environments, attackers may not need malware or encryption to create impact: One successful SSO login can enable rapid “smash-and-grab” access to high-value SaaS data—especially when audit logging is limited, disabled by default, or not centrally monitored.
This is primarily an identity and SaaS visibility problem. Collect and monitor SaaS audit logs for bulk downloads and unusual access, then couple that visibility with playbook-driven response for high-risk identity events (new MFA enrollment, anomalous sign-ins, and help-desk–driven changes) so suspicious sessions can be investigated and contained quickly.
Paid Operators, Higher-Pressure Vishing
ShinyHunters is scaling vishing-driven intrusions by outsourcing scripted, call-center–style tasks—and even harassment services—to paid contractors. The goal is likely to accelerate high-volume, low-cost pressure campaigns and coerce users into fast compliance by optimizing caller personas (including recruiting female callers). ShinyHunters calls this model the “SLH Operations Centre,” a vishing operation built for volume and speed.
Recruitment activity in ShinyHunters’ Telegram channel aligns with the campaign timeline and mirrors behavior we’ve previously observed. Operators appear to pay contractors to follow vishing scripts and handle related tasks, while also purchasing disruption services such as email bombing, call flooding, and SMS spamming. Payments are advertised in cryptocurrency, and the volume-based incentives suggest a model built to scale pressure tactics cheaply and quickly.
We also observed recruitment language explicitly seeking female callers (see Figure 2). While we cannot confirm intent, this may reflect testing which caller personas yield higher compliance during vishing attempts. A believable “support” or “help-desk” persona—delivered in a way that matches a target’s expectations—can lower suspicion and increase follow-through, a dynamic also seen in Scattered Spider vishing campaigns.
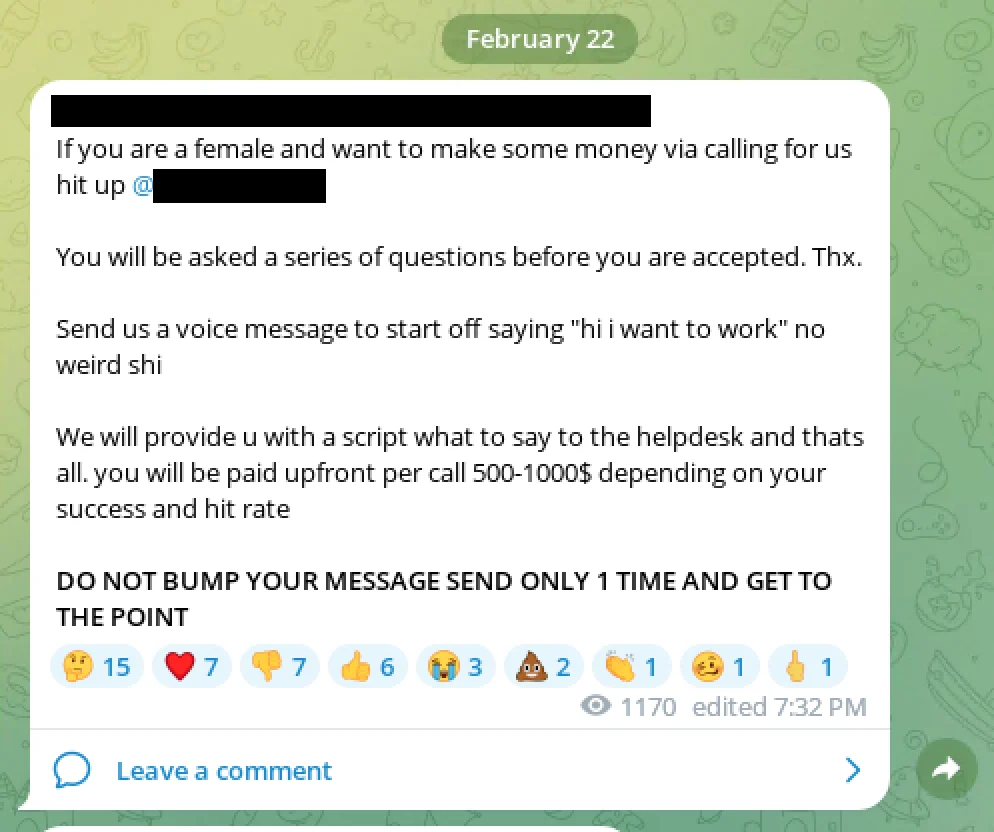
Figure 2: ShinyHunters recruiting female voice operators
This operating model mirrors broader cybercrime specialization, including ransomware-as-a-service (RaaS) programs, where core operators outsource high-volume, noisy work to contactors or affiliates while retaining the high-skill steps that create access and leverage.
For defenders, this translates to more frequent and coordinated social engineering waves and shorter decision windows for users and help desks. Rather than trying to block every call or message, prioritize controls that reduce “human pressure” failure points, such as strict help-desk verification, added friction for MFA resets, and rapid session containment when suspicious identity events occur. Where possible, automate correlation across the identity-to-SaaS chain and trigger response playbooks fast enough to contain access before it spreads.
Step Up Your Defenses Against ShinyHunters-Style Intrusions
ReliaQuest’s Approach
ReliaQuest GreyMatter helps security teams detect, contain, investigate, and remediate ShinyHunters-style intrusion paths by prioritizing the identity and SaaS signals that matter most.
GreyMatter Digital Risk Protection: Identifies and tracks external impersonation infrastructure, including newly registered lookalike domains and subdomain-based impersonation activity, to support early takedown and rapid blocking. It also proactively alerts on users that have names and other identifiers on the dark web to help detect potential targets early.
Agentic AI: Automatically investigates the full identity-to-SaaS attack chain after an initial signal (for example, suspicious sign-ins, MFA re-enrollment, or anomalous file download events), correlates downstream SaaS access, and can drive faster containment by escalating high-confidence incidents with clear next actions.
Detection Rules: Purpose-built detections designed to surface malicious activities like privilege escalation or persistence. These rules help spot unauthorized or anomalous behavior, including attempts to exploit legitimate applications and processes.
Detection rules work together with the following GreyMatter Automated Response Playbooks, which allow security teams to rapidly contain threats. When entire attack chains like the one in this report can execute in under an hour, cutting down mean time to contain (MTTC) to minutes is key in helping organizations substantially minimize the impact of an attack.
Terminate Sessions: Immediately revokes attackers’ access by invalidating credentials and ending all active user sessions.
Disable User: Automatically disables compromised user accounts to halt unauthorized activity and prevent further damage.
Your Action Plan
This activity shows ShinyHunters compressing the path from first contact to broad SaaS access by combining subdomain-based impersonation, vishing-driven pressure, and identity workflow abuse. Because attackers can achieve high impact without malware, prioritizing domain blocking alone is not enough. The actions below focus on preventing initial access, detecting session theft and identity tampering quickly, and limiting SaaS blast radius.
Adopt phishing-resistant MFA: Require phishing-resistant factors (for example, FIDO2 or WebAuthn security keys). Where feasible, bind sessions to expected IPs or locations and enforce risk-based step-up authentication.
Limit SaaS access by context: Enforce stronger Conditional Access controls for sensitive SaaS applications via SSO. If business operations don’t require CRM, ERP, or HR system access from untrusted locations, implement policies to block or require step-up controls.
Close the mobile visibility gap: Require conditional access for unmanaged devices, limit access to sensitive SaaS data from personal and mobile devices where possible, and ensure mobile sign-ins and sessions are logged and monitored.
What’s Next
ShinyHunters’ current infrastructure and operating model point to near-term shifts in how these campaigns will likely show up for defenders, and where common controls may fall short.
Current State | Next Likely Evolution | Why We Assess This | Impact |
|---|---|---|---|
Lookalike domains/subdomains | Greater reuse of shared attacker infrastructure (disposable subdomains and trusted-looking hosted pages) and migration across domain providers to complicate tracking. | Attackers will abuse what works, and there’s only so many domains that look realistic to an end user. We’ve also consistently seen threat actors move from providers to avoid detection and law enforcement tracking efforts. | Harder infrastructure tracking; higher click-rates on routine-looking domains. |
Live AiTM phishing | More mature phishing toolkits that support live session orchestration, with deeper customization for more believable pages to increase victim interaction. | Social engineering plus phishing toolkits is still relatively new. We’ve seen both tactics work individually with great success; combining them is a logical evolution but requires more custom tooling. | Faster initial access with fewer alerts—especially when victims are steered into low-visibility paths (mobile, Virtual Desktop Infrastructure [VDI], unmanaged networks). |
Manual use of CRM/ERP/HR data | More repeatable “targeting packs” and templated outreach that uses breach and system-of-record data to personalize pretexts | We’ve observed CRM and ERP data used as a targeting engine for follow-on social engineering, suggesting the approach can be templatized and scaled. Because these datasets are structured (CRM/ERP/HR systems of record), they’re easy to operationalize at scale. | Faster targeting and higher conversion; less time between data exposure and exploitation. |
IOCs
Artifact | Details | Artifact | Details |
acess-terms[.]com | Domain | help-okta[.]com | Domain |
okta[.]guide | Domain | desk-okta[.]com | Domain |
sso[.]guide | Domain | safe-okta[.]com | Domain |
okta[.]domains | Domain | prod-okta[.]com | Domain |
setup-okta[.]com | Domain | lock-okta[.]com | Domain |




