Introduction: 4-Minute Warning—Speed Wins When Identity Fails
Our Annual Cyber-Threat Report distills 365 days of frontline data into 1 strategic guide. We strip away the
noise to provide an evidence-based breakdown of the specific tactics, techniques, and procedures (TTPs) that
shaped the 2025 landscape. Use these insights to benchmark your security posture against real-world outcomes,
see where your defenses hold, and pinpoint what must change to stop the tactics that are working right now.
In 2025, AI contributed to the success of intrusions more than ever before. We saw adversaries weave AI and
automation into their tradecraft not just to move faster, but to generate convincing lures at scale.
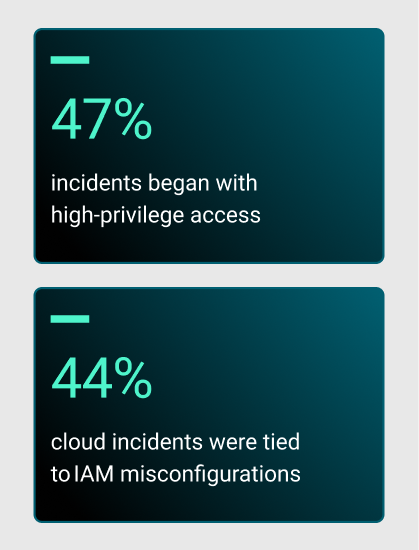
But AI wasn’t the only accelerant. Attackers also got more efficient at initial access by breaking trust
instead
of infrastructure. Through aggressive social engineering—from IT help-desk vishing to North Korean fake worker
schemes and “ClickFix” tactics—adversaries bypassed technical perimeters and secured valid credentials with
elevated privileges from the start.
With that foothold, many attackers no longer need to “smash and grab.” They live off the land, blend into
normal
traffic, and repurpose legitimate tools as weapons. For defenders, that means hunting for a single IOC quickly
becomes a dead end. Security has become less about spotting a malicious file and more about correlating
behavior
across users, endpoints, and cloud activity to catch the moment a trusted identity starts acting
untrustworthy.
These tactics are lowering breakout times and raising the stakes for defenders. This year, we saw average
breakout time—the interval between initial compromise and lateral movement—drop by 29%, from 48
minutes
to 34
minutes. But some attackers are moving much faster than the average. The fastest intrusions reached
lateral
movement in just 4 minutes and achieved data exfiltration in 6 minutes
post-entry.