What Happened to Black Basta's Playbook?
The Automated Teams Chat Phishing Threat Hitting Executives

Resources: https://linktr.ee/ReliaQuestShadowTalk
Black Basta disbanded in February 2025, but their playbook didn't go with them. In March 2026, 77% of observed incidents targeted executives and directors, and attackers moved from first contact to malicious script execution in as little as 12 minutes. The tactic has been automated, refined, and is now running faster than most SOCs can respond.
Join hosts Alexandra and John as they discuss:
- How attackers leverage Microsoft Teams phishing to target high-privilege accounts with alarming speed
- Why automation is compressing attack timelines and sharpening target selection
- The controls that can stop it, from help desk verification to automated containment workflows
Two questions your organization should be asking right now:
- When IT requests remote access to a senior leader's endpoint, is identity verified through a channel separate from the one the request came from?
- Do your highest-privilege accounts have dedicated automated containment workflows — or are they the gap in your response playbook?
John Dilgen: Cyber Threat Intelligence Analyst at ReliaQuest, where he specializes in researching cyber threats impacting ReliaQuest customers. With a strong technical background, he previously served as an Incident Response Analyst and Trainer at ReliaQuest.
Alexandra Moore: Manager of Threat Intelligence at ReliaQuest, where she leads intelligence analysis and customer dissemination to help organizations understand and respond to emerging cyber threats. Prior to this, she established and scaled monitoring across Russian-language cybercriminal platforms at Digital Shadows, building collection and analytical coverage to support digital risk protection capabilities.
Additional Content
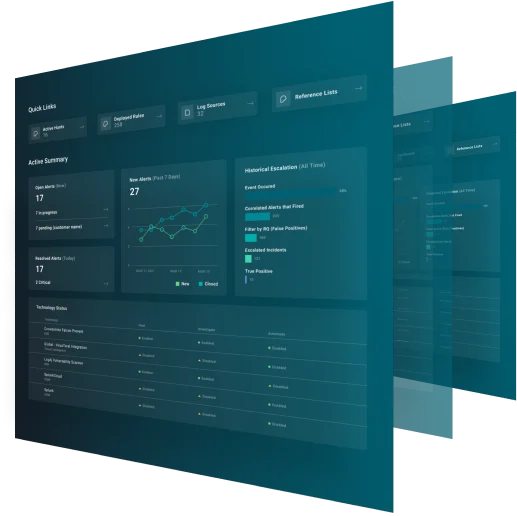
What is GreyMatter?
GreyMatter is an agentic AI security operations platform that enables security teams to detect threats at the source, contain them in under 5 minutes, and eliminate Tier 1 and Tier 2 security operations work for faster investigation and response across cloud, hybrid and on-premises technologies.