Turning One Environment’s Threat Signal into Network-Wide Immunity
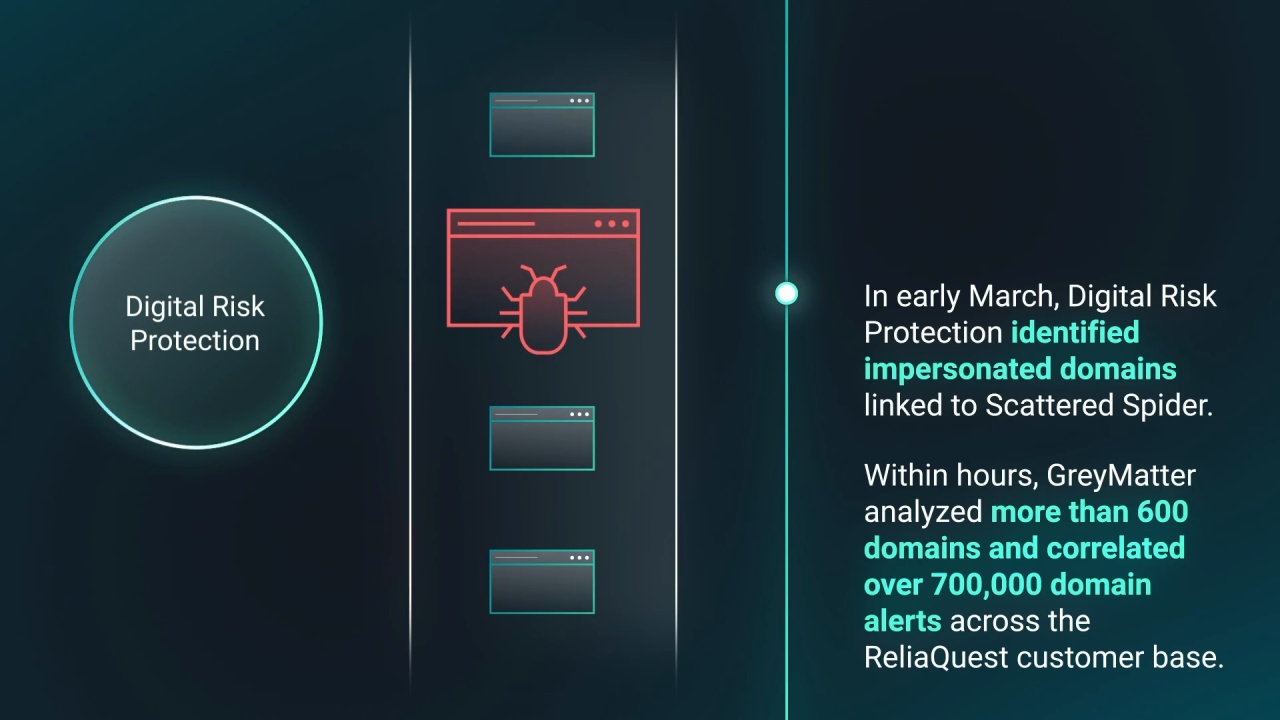
Threat actors like Scattered Spider operate on compressed timelines. They exploit SaaS and identity systems to harvest credentials and secrets, then use legitimate access to move laterally, allowing them to complete campaigns in hours instead of days.
For most SOCs, this creates an impossible gap. Tool-by-tool investigation, delayed threat intelligence, and reactive detection engineering means defenders are responding after access has already been established.
The challenge is no longer just seeing threats as they happen. It’s about anticipating them—getting ahead of attackers in time to prevent their impact.
Cybersecurity is a team sport. The more we collect and distribute intelligence, the more we can prepare for threats, and the better protected we all are.
We’ve built that principle into the GreyMatter agentic AI security operations platform.
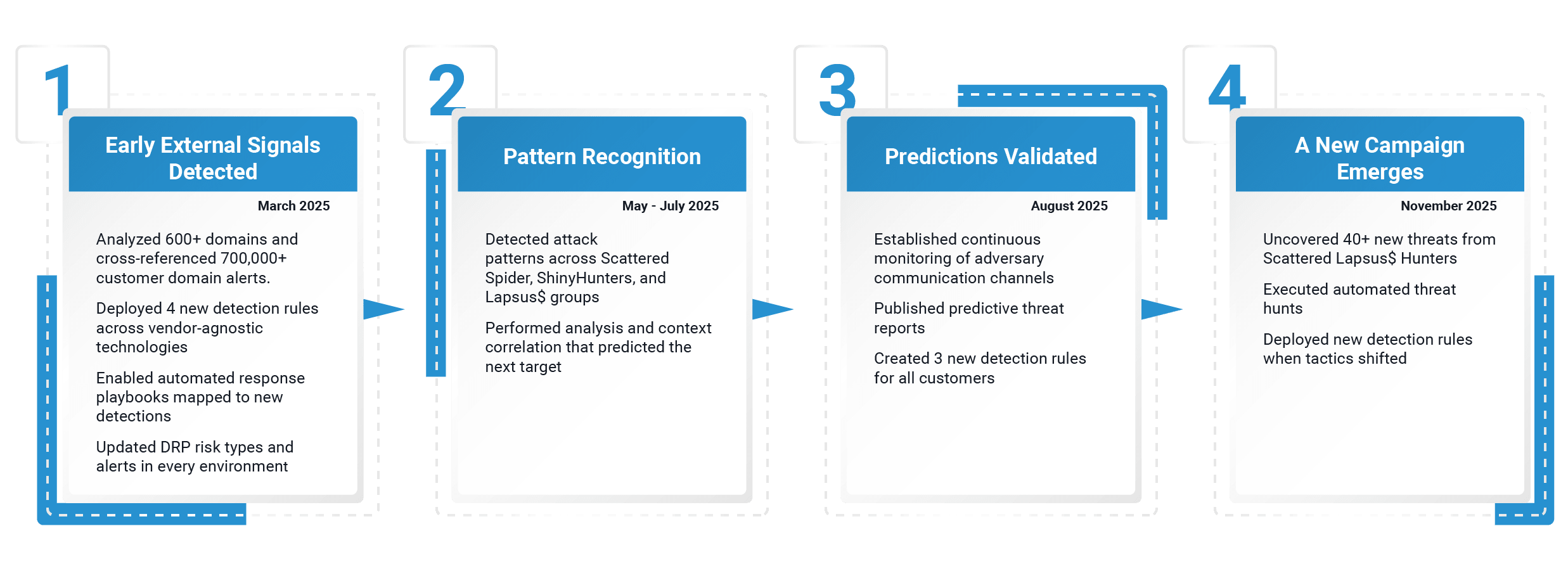
This guide walks through a specific use case: How the GreyMatter “network effect” defended customers against Scattered Spider activity in 2025—turning early signals into proactive, predictive defense across our customer base while tailoring controls to each environment.