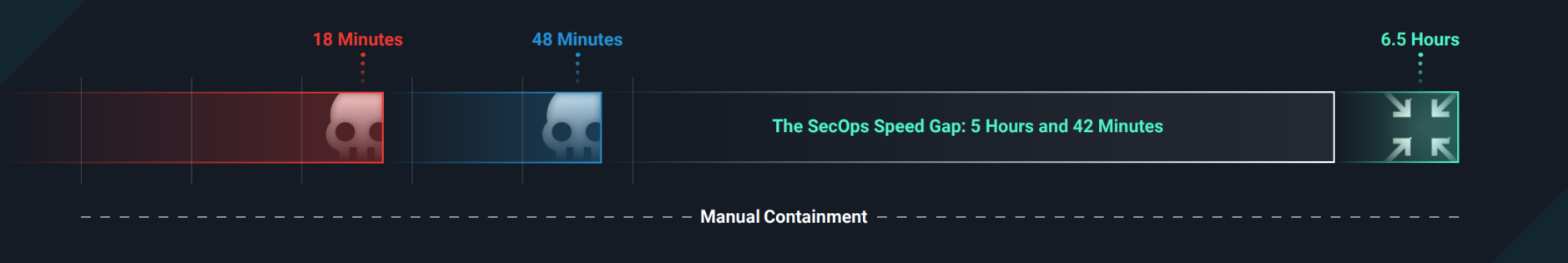
When attackers can establish persistence faster than your team can detect them, the math becomes impossible to ignore. Your security needs automation.
This guide provides a framework to automate strategically: knowing what to automate, when to automate it, and how to stay in control while building speed. Because at 18-minute breakout times (or faster), manual response isn't just slow. It's obsolete.
Automating Cybersecurity Playbooks
A cybersecurity playbook serves as the foundation for a well-prepared security operations team, comprising a set of guidelines, procedures, and best practices meticulously designed to respond effectively. Automating these playbooks elevates your capacity to respond quickly, consistently, and efficiently.
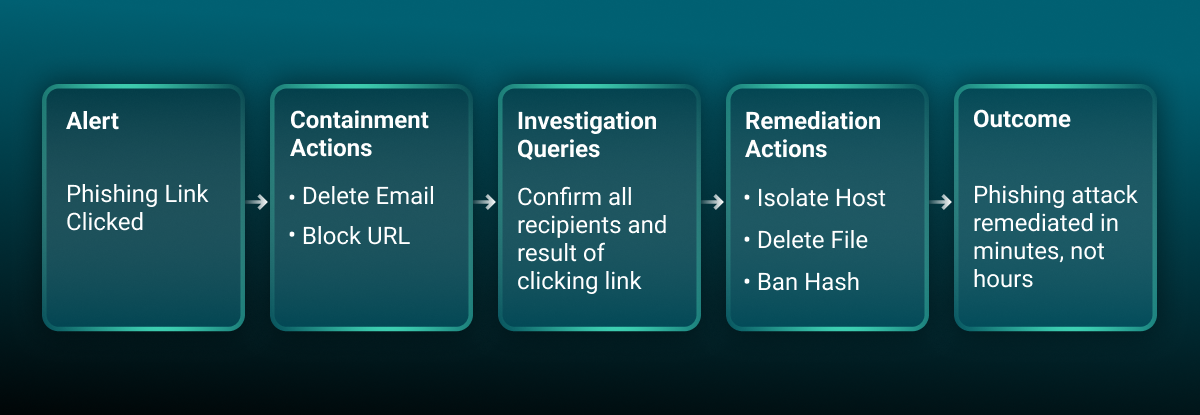
Automated Playbook: Phishing Link Clicked
Phishing is a top attack vector, which means it’s critical to respond as fast as possible when a phishing detection fires. Security teams can respond faster by implementing automations that can analyze user-reported emails and respond to clicks in seconds. Here’s what an automated playbook might look like for a common phishing detection—Phishing Link Clicked—broken out into actions for containment, investigation, and response.