What is Security Automation?
Security automation applies software to streamline the time-consuming, manual processes of cybersecurity. As advanced attackers leverage AI and automation to exploit vulnerabilities like over-privileged roles, which include 99% of cloud identities, security operations teams need enhanced capabilities to scale their defenses.
Modern security automation extends beyond simple PowerShell scripts for faster tasks; it involves leveraging artificial intelligence (AI) and machine learning (ML) for sophisticated threat detection, investigation, and response. The primary advantage is executing these tasks with greater speed, accuracy, and at scale.
Understanding Security Automation
Many organizations underestimate the range of security tasks that can be effectively automated. The following table illustrates prime candidates for security automation across common Tier 1 and Tier 2 tasks, detailing how automation delivers value.
Investigation Tier | Security Task | How It’s Automated |
Tier 1 | Enriching alerts with context | Alerts from various sources (email, EDR, XDR, SIEM, SOAR) are automatically enhanced with relevant data (asset/user data, threat intelligence via API integrations). |
Deduplication and filtering false positives | Automation removes duplicate alerts and suppresses identified false positives before human review. | |
Basic remediations | Low-investigation tasks like quarantining known malicious processes or mitigating phishing emails are executed automatically through playbooks. | |
Preliminary decision-making | AI/ML identifies patterns to make initial judgments – escalating malicious activity for human intervention or auto-remediating benign anomalies. | |
Tier 2 | Gathering telemetry across tools | Eliminates manual swivel-chair investigations by stitching together data from cloud logs, network logs, endpoints, and identity systems. |
Link alerts to historic data and threat intelligence | Determines if activity connects to known threat actors, past network behaviors, or correlates with vulnerability exposures. | |
Orchestrating multi-step workflows | Executes complex, multi-tool workflows for in-depth triage, such as quarantining a host, blocking a hash, and alerting the SOC for ransomware. | |
Generate detailed reports | Produces summaries of incident tickets and provides clear explanations for actions taken, ready for review. |
AI’s Role in Security Automation
AI significantly enhances everything within the process of automating security tasks. It adds the ability to generate and synthesize information into the automation mix and allows security teams to perform higher-level security functions at scale.
By leveraging machine learning to detect and pick up patterns, AI transforms static “if this, then that” actions into dynamic, multi-step chains. As AI/ML models continuously learn and improve, the results and effectiveness of those automated workflows – known as automated response playbooks – become increasingly accurate over time.
What Are Automated Response Playbooks?
AI can be applied to security automation to orchestrate and streamline multi-step automated response playbooks. The table cited one example of ransomware response; the same principle of automated security orchestration can also be applied to cloud security.
For instance, when suspicious cloud activity is detected - such as multiple failed login attempts followed by a login from a foreign IP – an automated response playbook can:
Validate the alert, enriching it with known device fingerprints and authentication history.
Query related activity, like privilege escalation attempts and data access patterns.
Contain the impact by forcing an immediate password reset via API and disabling the affected credentials.
Block the foreign IP address at the level of the identity provider or firewall.
Notify the security analyst with automated alerting of the incident, complete with an incident report containing correlated indicators and suggestions for next steps.
Transforming Business Operations with Security Automation
Organizations typically observe several indicators signaling a need to advance their security capabilities with automation.
How to Know When Your Organization is Ready for Security Automation
These indicators suggest your company's security strategy is straining under current demands and could improve with security automation:
Overworked SOC: Analysts grapple with alert fatigue and crushing workloads; 63% say they are experiencing some level of burnout.
Ignored Alerts: With nearly 4,000 security alerts daily, research indicates 62% are getting ignored. This approach cannot effectively counter potential security events or evolving threats.
Excessive Triage Time: Analysts spend an average of 3 hours a day triaging alerts. With automation, that number could be cut down to minutes.
Compliance Challenges: Increasing cybersecurity compliance demands leave less than half of organizations feeling prepared. Automating tasks can help meet new security compliance expectations.
How to Maximize Value from Business Security Automation
Security automation achieves its greatest value when combined with the right data and capabilities. AI/ML capabilities are fundamental for preventing modern cyberattacks at scale. For the most robust security automation performance, AI integration is essential. The following capabilities are highly recommended to achieve optimal security automation performance.
Centralized Telemetry: AI requires comprehensive data to operate effectively. SIEMs or other log aggregation platforms may be necessary to collect and consolidate diverse data sources.
How it Helps: This foundational data enables comprehensive threat detection, correlation, and analysis across the entire IT ecosystem, eliminating blind spots.
Endpoint Solutions: For robust endpoint protection, AI tools need the ability to reach the endpoint and access its telemetry.
How it Helps: This capability is crucial for querying, detecting lateral movement, and isolating compromised assets.
Network and Cloud Data: Cloud audit trails and network infrastructure data (from firewalls, proxies) combine with endpoint data to eliminate detection and protection blind spots.
How it Helps: This integration provides a holistic view of activity across hybrid environments.
Identity Systems: Identity telemetry (IAM, Directory, cloud identities) is key for spotting early signs of intrusion or account compromise.
How it Helps: Monitoring identity interactions is often the first line of defense against unauthorized access.
Threat Intelligence Feeds: Proprietary, commercial, and open-source feeds provide vital context and indicators of compromise (IOCs).
How it Helps: Integrating these feeds allows automated systems to proactively identify and block known threats.
Cybersecurity Testing Tools: Vulnerability scanners, network sniffers, and code analysis tools are valuable sources of threat data for ingestion, correlation, and context.
How it Helps: Tools like Nmap, Metasploit, and Burp Suite provide crucial insights into an organization's attack surface.
Cloud and SaaS Telemetry: Cloud and SaaS environments form a major part of the modern attack surface (e.g., AWS CloudTrail, GCP audit logs).
How it Helps: Collecting this telemetry is essential for detecting threats within dynamic cloud infrastructures.
Security automation can benefit organizations of all sizes, and AI capabilities extend to any SOC or stack, regardless of its current maturity.
Real-World Examples of Security Automation in Business
While more threat data generally improves outcomes, security automation can be implemented for businesses of all sizes and industries. Here are a few examples showcasing its impact:
Small Businesses: Out-of-the-Box Functionality. Small teams often operate with lean resources in terms of time, tools, and experience. Pre-built automation workflows infuse sophistication, expertise, and efficiency into their security strategies, enabling analysts to achieve immediate productivity.
Mid-Sized Businesses: Unified Tool-Stack Integration. These companies frequently contend with tool sprawl, facing abundant data but insufficient time. Automation aggregates, normalizes, and correlates telemetry from all available sources, preparing it efficiently for SOC review.
Large Enterprises: Massive SOC Workflow Automation. Large organizations face the challenge of rapidly detecting potential threats across vast, complex architectures where attackers can easily hide. AI-powered automated SOC workflows reduce response times across large environments, mitigating and containing threats within minutes.
Implementing Security Automation: A Strategic Approach
How do security leaders take their organizations from manual security operations to highly automated processes?
Here are 5 initial steps:
Define Need: Identify where your organization requires security automation most. Your specific needs will depend on company size and current security pain points, such as excessive alerts, overwhelming threat data, or a lack of specialized expertise.
Establish Compatibility: Determine which of your existing solutions support the functions you aim to automate. Those stay. Now identify vendors that integrate seamlessly with your current stack.
Implement Training: Even with automated workflows, ensure comprehensive training. Plan a period for onboarding – the more intuitive the tool, the shorter this period will be. Crucially, gather feedback from experts who previously performed these functions manually; their insights are invaluable as they use the automated functionalities daily.
Consider AI Integration: Automation forms the foundation, but for future-proof security, AI/ML is increasingly essential. Partner with a vendor that supports AI-powered workflows and machine learning capabilities for optimal performance and adaptability.
Articulate Business Value: When presenting new automated security systems to leadership, emphasize financial benefits. Highlight not only immediate SOC cycle savings but also future reductions in training and upskilling costs, alongside substantial savings from preventing potential breaches due to superior detection and incident response rates.
Lastly, garner feedback. You are asking experts who have previously done these security functions manually and know them inside and out. Their opinions will be the most valuable as they are now the ones using the automated functionalities every day.
Address Security Automation Challenges Early, and Head On
Everything worthwhile takes a bit of investment—and some caution. Here are seven things to watch out for as you begin your security automation journey.
Avoid Over-Automating Everything at Once: Allow your teams to get used to one new security automation use case at a time to make sure changes stick.
Plan for Growth: Don’t only look at what integrations work with your stack now; keep in mind growth and choose a vendor with flexibility and a roadmap for future growth and evolving stack requirements.
Automate to Enhance, Not Replace: Automation significantly enhances capabilities, yet human expertise remains vital for nuanced judgments and strategic oversight. It empowers teams of any size to meet complex security demands.
Factor-In AI from the Start: Automation without AI/ML is not enough to defend against advanced threats. Choose a vendor that provides robust AI-powered workflows and ML capabilities for the possible performance.
Focus on Impact: When pitching a new automated security system to higher-ups, present it in terms of money saved, not spent. Security automation not only saves SOC cycles now, but training and upskilling costs in the future—as well as money saved on potential breaches due to superior detection and incident response rates.
Maximizing Long-Term Value from Security Automation
Implementing security automation can feel like a win in itself, and it is. But the purpose is to drive permanent results, not just temporary efficiencies.
Here are important post-adoption considerations for long-term success:
Ensure Stakeholder Alignment:
In larger organizations, security responsibilities are often distributed. To achieve measurable results, all key stakeholders must be trained on new products, dashboards, and workflows, ensuring consistent execution.
Monitor Data Inputs:
Especially with AI/ML, the solution evolves with the data it receives. Ensure feedback is consistently provided, and investigations are properly resolved and logged, giving the model accurate information to learn from.
Measure and Communicate Success: Leverage automated reporting to demonstrate improved security posture and financial benefits to board members, clients, and your internal team.
Board Members: Quantify cost savings through metrics, like hours saved in investigations.
Clients (for MSSPs): Emphasize reductions in false positives, showcasing how much work is alleviated for client SOCs.
Team: Highlight hours saved on manual tasks like aggregating, correlating, and enriching alerts, allowing them to experience the benefits directly.
By consistently highlighting successes and proactively integrating your security automation program into your operational framework, you significantly increase its long-term impact and potential to transform security operations.
ReliaQuest’s Unified Approach to Security Automation
ReliaQuest provides industry-leading cybersecurity automation for businesses of all types.
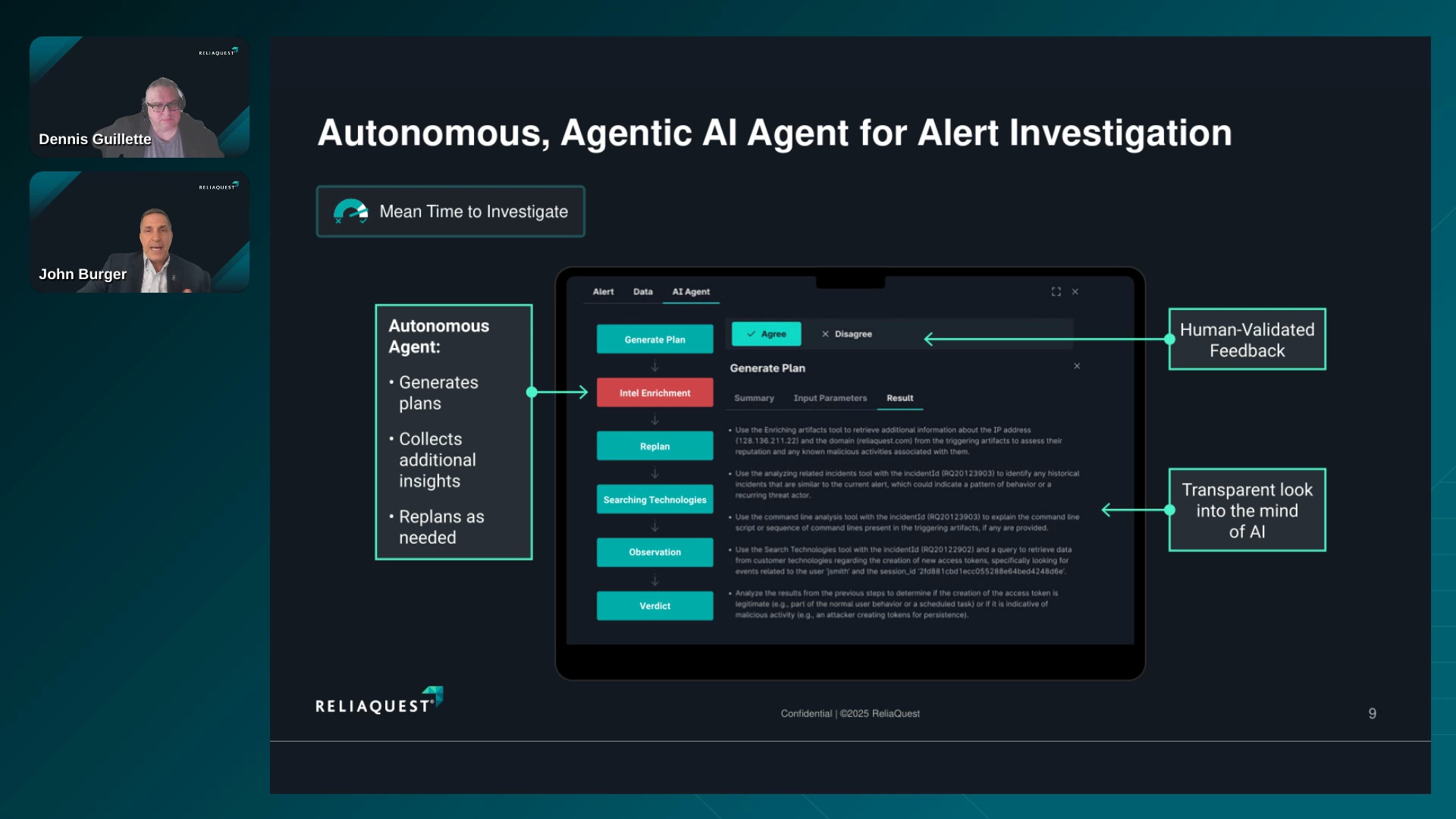
With ReliaQuest, enterprise security teams automate time-consuming Tier 1 and Tier 2 security operations tasks with its Agentic AI Security Operations Platform,GreyMatter.
GreyMatter leverages automation and agentic AI to relieve even more of the security burden from overwhelmed SOCs and facilitate automated detection and response.
For example, with GreyMatter, agentic AI empowers security teams to automate investigations, providing unique benefits like:
Threat Containment in Minutes: Agentic AI delivers automated remediation by analyzing alerts, correlating them with threat data, and taking containment actions to stop known malware, phishing attacks, and other predictable cyber threats—all without human intervention.
Reduction of Tier 1 and Tier 2 Tasks: Analysts are freed to focus on critical decisions and active threat hunting. Agentic AI-powered GreyMatter acts as an "entry-level security analyst," eliminating repetitive tasks like deduplication, alert vetting, and initial investigations with superhuman speed and accuracy.
Prioritization of Business-Centric Security Choices: As CISOs are increasingly required to justify security decisions based on business impact, GreyMatter provides a strategic advantage. Prioritization is based on business context, not solely on flat indicators like CVSS scores. This ensures security threats affecting business-critical assets are brought to the forefront, enabling leaders to act strategically.
Security Automation: The Foundation for Future-Proof Security
Security automation is the critical first step in building a future-proof security foundation. By integrating automation with advanced technologies like AI, ML, and Agentic AI, organizations can offload day-to-day security tasks. This empowers SOCs to focus on strategic, proactive initiatives such as threat hunting, enabling teams of any size to effectively manage the demands of a growing attack surface at scale.