What is Preemptive Security?
Modern attackers achieve lateral movement within a breached network in 18 minutes. Merely reacting to incidents can’t keep up with that kind of speed.
Preemptive security applies advanced technologies – like AI in cybersecurity, predictive threat intelligence, and automated response – to anticipate, identify, and neutralize risks before they become breaches.
Don’t think of preemptive security as a replacement of traditional threat detection, investigation, and response (TDIR); think of it as a redefinition. In a preemptive model, detection begins with continuous visibility, where investigations are enriched automatically with context from threat intelligence, and responses fire at machine speed. The result: faster and smarter threat, detection, investigation and response (TDIR) that denies adversaries the time and space they need to succeed.
What’s the Difference Between Preemptive and Reactive Security?
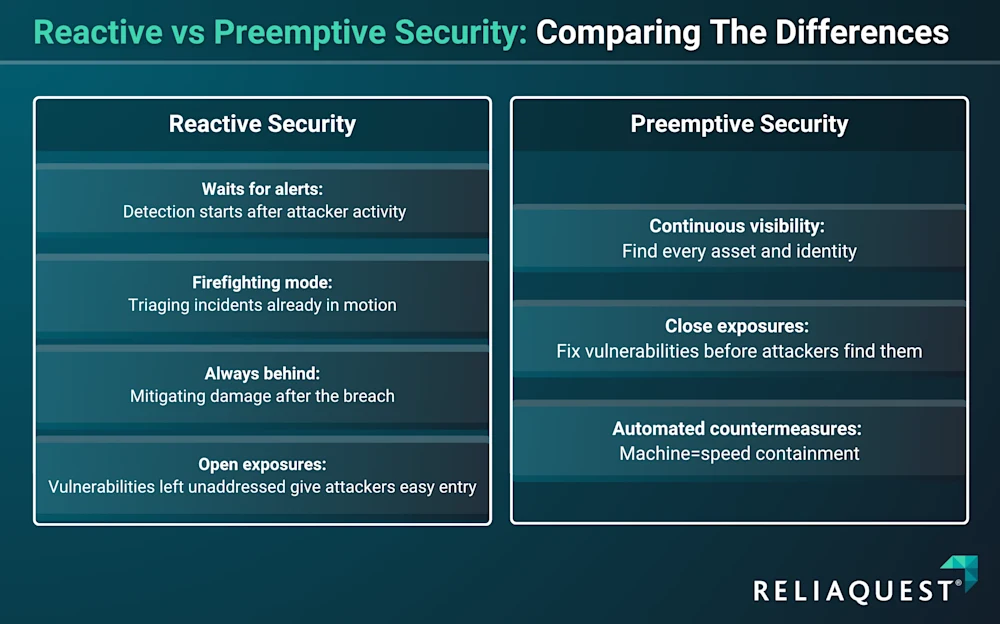
Reactive security waits until a risk has escalated into a threat and is already in motion within your environment. It involves responding to an incident alert, triaging the incident, and containing attackers once they’re already inside a network. Fundamentally, it’s damage control. It’s essential, but it’s always a step behind.
Preemptive security is different by focusing on preventing breaches from happening in the first place. Instead of waiting for attackers to exploit your bling spots and vulnerabilities, it scans the global attack surface grid (GASG) to resolve risk before attackers can exploit them, uses predictive threat intelligence to spot emerging threats, and employs deception technologies to divert attackers into decoys, keeping them away from critical assets and blocked from re-entrance.
Why Does Preemptive Security Matter for Enterprise Security Operations?
Preemptive defense assumes you can take the hit and recover quickly. That assumption no longer holds up. Modern attackers, especially those using AI, exploit vulnerabilities in ways and at speeds that make traditional models obsolete.
According to a Gartner Preemptive Security report, by 2030 preemptive defense will account for more than 50% of IT security spending, up from less than 5% in 2024. That’s because reactive security alone is no longer viable against AI-driven attackers.
Preemptive security is the only way to keep up.
How Are Attackers Using AI? And Why Do Defenders Need It?
AI for cybersecurity is no longer optional. AI has enabled attackers to move faster, skip around defenses easier, and launch attacks at a greater scale and speed than ever before. These tools can automate reconnaissance, generate phishing campaigns that adapt in real time, write polymorphic malware to bypass traditional defenses, and even create deepfakes to trick unsuspecting users.
Without preemptive security, enterprises are unable to protect against breaches.
How Can Preemptive Security Elevate Analyst Impact Beyond Firefighting?
Most SOCs are drowning in alerts and repetitive tasks. Most SIEMs generate thousands of alerts every day, leaving analysts with no time to investigate them. In reactive models, analysts are stuck firefighting instead of improving strategy.
Preemptive security automates Tier 1 and Tier 2 tasks, meaning dwell time drops from hours to minutes, and high-confidence signals from decoys or predictive intelligence can cut false positives dramatically. Instead of firefighting, analysts shift to higher-value work like detection engineering, adversary emulation, and proactive threat hunting – the activities that strengthen resilience over time.
Why Does Compliance Now Require Continuous Validation?
Annual penetration tests and quarterly audits once satisfied boards and regulators. That’s no longer the case. Under NIS2 and DORA, organizations must demonstrate ongoing control effectiveness.
Reactive models can only show how quickly you responded after an incident. Preemptive models embed validation into daily operations: continuous breach simulations, automated red-teaming, and real-time reporting that proves defenses are effective under real-world conditions. This not only satisfies regulators but also provides boards with tangible, continuous assurance that investments are working as intended.
How Does Preventing Breaches Protect Customer and Investor Trust?
Every breach can damage credibility with customers, partners, and investors. Reactive response means stakeholders learn about incidents after the fact. Preemptive security prevents many incidents outright, reinforcing trust and protecting reputation.
What Are the Benefits of Preemptive Security Operations?
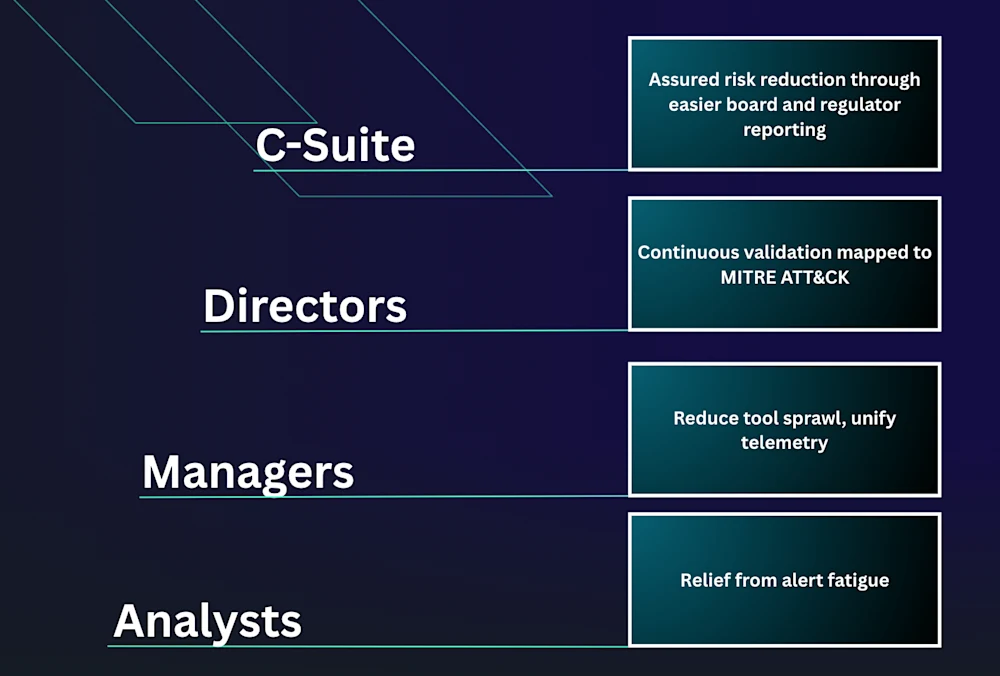
Preemptive cyber defense delivers outcomes across roles that reactive approaches will never achieve. Instead of chasing alerts after attackers are already inside, it closes exposure windows, reduces operational drag, and measurably proves resilience.
How Does Preemptive Security Benefit the C-Suite?
For executives, the value is direct and strategic: reduced breach probability and reputational risk. For example, exposures account for 92% of ransomware entry points, often via shadow IT or forgotten SaaS integrations, while 69% of organizations have experienced cyber attacks exploiting unknown, unmanaged, or poorly understood assets.
Preemptive models continually surface and remediate those blind spots before they become crises. That translates into fewer emergency board calls, smoother compliance audits, and stronger negotiating positions with cyber insurers.
How Does Preemptive Security Benefit Directors?
Board and risk leaders see where dollars map to outcomes. Instead of slide decks full of tool logos, preemptive operations deliver unified reports tied to MITRE ATT&CK techniques, showing which attack paths their teams have blocked, which playbooks have fired, and which vulnerabilities they have eliminated.
Ultimately, this means that directors can track real progress over time – like reducing mean time to contain (MTTC) from days to hours – and connect it directly to enterprise risk reduction.
How Does Preemptive Security Benefit Managers?
For security leaders, efficiency is the key payoff. They replace tool sprawl and siloed workflows with fused telemetry and intelligence. Instead of bombarding managers with 1000 medium-severity vulnerabilities, preemptive models highlight the five that map directly to exploitable paths an attacker could actually use tomorrow. Automation handles the containment of routine events, while managers can focus scarce human resources on strategic improvements and incident readiness.
How Does Preemptive Security Benefit Analysts?
For analysts, preemptive defense makes the difference between drowning in alerts and doing meaningful work. Automated workflows handle containment in minutes instead of hours, shrinking MTTC from 6.3 hours to as little as 3 minutes. Deception systems flag attacker interaction with decoys at high confidence, meaning analysts don’t have to wade through false positives - that frees them to focus on proactive threat hunting, detection engineering, and adversary emulation - the proactive work that improves resilience over time.
What Are the Key Components of a Preemptive Cybersecurity Strategy?
CAASM
Cyber Asset Attack Surface Management (CAASM) delivers continuous, unified visibility into assets, identities, and exposures. It does this by answering critical questions like “What do we own?” and “Where are we exposed?”. CAASM helps eliminate blind spots that adversaries exploit. Integrated with SIEM, EDR, and vulnerability scanners, it ensures SOC teams aren’t operating with partially outdated inventories.
This visibility lays the foundation for TDIR by ensuring detection and investigation start with a complete, accurate picture of the environment.
Integrated Threat Intelligence
Threat intelligence fuels preemptive defense and makes it actionable. Strong integration allows SOC teams to:
Automate Defensive Actions: When new indicators of compromise (IoCs) match known threat artifacts, automated playbooks can execute actions like blocking domains, revoking credentials, or isolating systems automatically.
Prioritize Resources: Intelligence fused with internal telemetry highlights which exposures attackers are most likely to exploit, so teams can focus efforts and resources where they matter most.
Inform Predictive Defenses: By analyzing attacker tactics, techniques, and procedures (TTPs), AI can simulate what the next wave of attacks might look like and create predictive threat intelligence that stops attackers in their tracks.
Within TDIR, integrated intelligence enriches investigations with context, shortening time-to-understanding, and making response actions more precise.
Behavioral Analytics and UEBA
User and Entity Behavior Analytics (UEBA) is the early warning system in a preemptive defense model. It continuously monitors logins, file transfers, application usage, and device activity to establish a baseline of user behavior and:
Detect Deviations: If an account, for example, suddenly accesses sensitive data it’s never touched before, or a device starts communicating with an unknown external server, UEBA flags it as high risk.
Reduce False Positives: Behavioral context helps distinguish malicious activity from legitimate but unusual behaviors, ensuring analysts can focus on genuine threats.
Ultimately, UEBA ensures defenders can catch attackers who have bypassed perimeter defenses before they can escalate privileges or move laterally.
This accelerates detection in the TDIR lifecycle, surfacing risky activity earlier in the kill chain and reducing the burden of long investigations.
Reporting and Frameworks
Preemptive security also helps prove effectiveness. Reporting aligned to established frameworks provides the necessary evidence.
MITRE ATT&CK mapping shows exactly where defenses are strong or weak across the attack lifecycle.
Regulatory alignment ensures compliance with standards like NIST, PCI DSS, or GDPR.
Operational dashboards translate technical performance metrics, such as mean time to contain (MTTC) or mean time to respond (MTTR) into business risk metrics that boards and regulators understand.
By measuring against common frameworks, organizations validate that preemptive measures actually function in real-world conditions.
For TDIR, these reports provide feedback loops that show whether detection, investigation, and response are improving over time and reducing enterprise risk.
AI and Automation
Preemptive cybersecurity defense cannot exist without AI and automation. Attackers are already using AI to scale reconnaissance, phishing, and malware faster than humans can keep up. The only way to close that gap is by deploying AI on the defense—and that involves combining proactive and reactive approaches to security operations.
This is where TDIR transforms most dramatically: automation collapses detection, investigation, and response timelines from hours to minutes, closing the attacker’s window of opportunity.
How Can I Implement Preemptive Security Solutions?
Moving from a reactive to a preemptive model involves fundamentally shifting how security operations are designed. This process begins with asking the hardest question of all:
“How do we find our blind spots? The things we don’t know we don’t know?”
Without surfacing hidden assets and exposures, even the best strategies risk leaving doors open for attackers.
This is why discovery and visibility are so important. Enterprises must continuously map every asset, identity, and connection across cloud, multicloud, SaaS, IoT, and APIs. Traditional Cyber Asset Attack Surface Management (CAASM) isn’t enough; it must be paired with continuous validation - because annual audits leave months of exposure. Regulators now expect daily proof that defenses work, and only preemptive operations can deliver it.
This is your foundation of preemptive defense.
Gartner’s 3D model of Deny, Deceive, and Disrupt provides the framework for acting on this visibility:
Deny means closing doors before attackers find them, enforcing zero trust, obfuscating sensitive resources, and using automated exposure management to shrink the window of opportunity.
Deceive lures adversaries into decoys and constantly moves critical assets that could be targets, turning reconnaissance into a trap and giving defenders valuable insight into attacker behavior.
Disrupt is where intelligence and automation converge, with predictive threat intelligence fusing external data with internal telemetry to inform detections and playbooks that can automatically contain or remediate threats before they escalate.
It’s important to reinforce these principles through continuous validation, such as with breach and attack simulations (BAS) and ongoing testing to prove to auditors that defenses are firing as they should – and through measurement that ties outcomes to business risk. Metrics like MTTC, false positive rates, and coverage across MITRE ATT&CK make progress tangible to CISOs and boards.
What Are the Challenges and Considerations of Implementing Preemptive Security
While these steps should ensure a successful preemptive security implementation, organizations will face other challenges. Keep an eye out for:
Tool Sprawl and Integration Gaps: Unified telemetry is crucial to preemptive defense. Siloed tools and disjointed workflows make it impossible to act at machine speed.
Overreliance on Point-in-Time Testing: Quarterly pentests or annual audits leave months of potential exposure. Continuous validation is the only way to maintain preemptive readiness.
Cultural Resistance: Shifting from a reactive mindset requires buy-in across leadership and SOC teams. Preemptive security solutions change how people work, not just what tools they use.
Autonomy and Oversight Imbalances: Where should you draw the line between human and machine-made decisions? For example, AI can automatically isolate a compromised endpoint showing malware behavior, but disabling a CFO’s business account during business hours should still require human approval.
Skills and Staffing: Even in AI-powered preemptive models, humans are critical for strategy, detection engineering, and incident analysis. Upskilling and role clarity are part of any transition.
Artificial Intelligence and Cybersecurity: Driving the Future of Preemptive Defense
AI in cybersecurity is what makes preemptive cyber defense viable. Attackers are already using AI to supercharge their operations - without AI on the defensive side, enterprises are stuck reacting at human speed to machine-speed attacks.
Looking ahead, Gartner predicts the emergence of an Autonomous Cyber Immune System (ACIS) -adaptive defenses that continuously learn and respond across the global attack surface grid. It’s a glimpse of where preemptive cybersecurity is headed, and a warning that enterprises must act now to prepare.
In a preemptive model, AI plays three distinct but complementary roles:
Preparation: AI can process huge volumes of threat intel, historical attacks, and telemetry to create detection logic, playbooks, and policies before attackers strike. This transforms data into readiness.
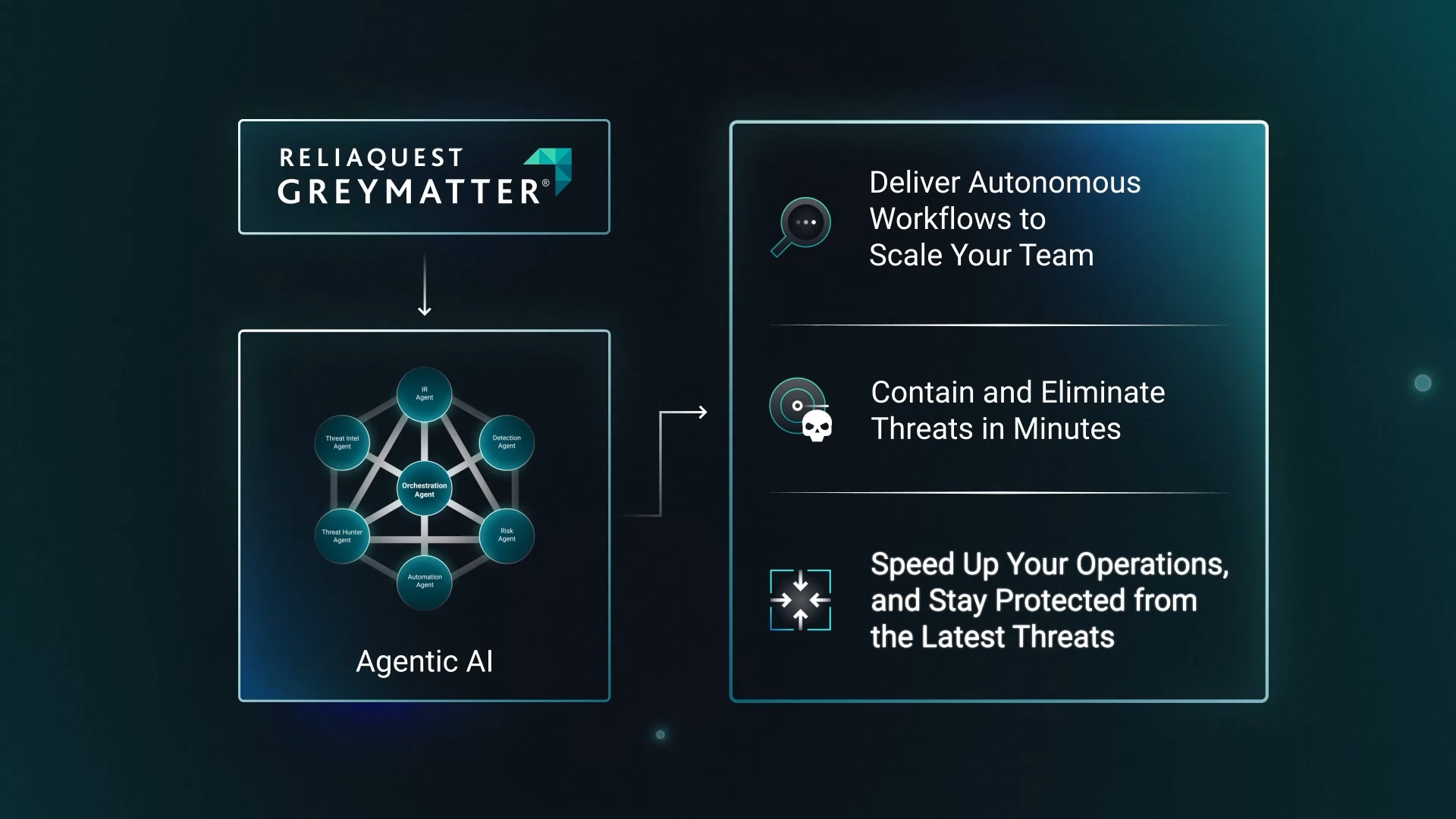
Response: Agentic AI teammates triage alerts, correlate signals across environments, and execute predefined playbooks in seconds. By taking over Tier 1 and Tier 2 workloads, they shrink time-to-containment and give analysts breathing room to focus on threat hunting and strategy – elevating SOCs beyond firefighting.
Support: Enriching alerts with external and internal context, auto-summarizing incidents for faster investigations, and mapping detections to MITRE ATT&CK so analysts can immediately see relevance and coverage.
This combination of preparation and real-time action is how preemptive defense beats cybercriminals at their own game. ReliaQuest GreyMatter operationalizes this dual role by unifying visibility, applying AI to enrich detections, and empowering SOCs with autonomous teammates that act across SIEM, EDR, cloud, and identity environments.
This product demonstration shows how GreyMatter Agentic Teammates can multiply your security teams’ impact instantly and exponentially.
What Tools and Technologies are Needed for Preemptive Cyber Defense?
While tools are important, building a preemptive security model is more about weaving together the right mix of capabilities into a unified, intelligent ecosystem. Critical layers include:
Endpoint and identity monitoring to catch credential abuse and lateral movement.
Behavioral analytics to detect anomalies that signature-based tools miss.
Email and phishing defenses to counter increasingly AI-driven phishing and social engineering campaigns.
Network and cloud-native controls to enforce segmentation and minimize blast radius.
Integration is the key challenge here. Tools in silos don’t add up to preemptive defense. ReliaQuest GreyMatter solves this by being technology-agnostic - stitching together telemetry from across your stack to provide a single, unified picture of risk and the automated workflows to act on it.
Ready to see how GreyMatter Discover integrates seamlessly into your existing stack?
What Tools and Technologies are Needed for Preemptive Cyber Defense?
While tools are important, building a preemptive security model is more about weaving together the right mix of capabilities into a unified, intelligent ecosystem. Critical layers include:
Endpoint and identity monitoring to catch credential abuse and lateral movement.
Behavioral analytics to detect anomalies that signature-based tools miss.
Email and phishing defenses to counter increasingly AI-driven phishing and social engineering campaigns.
Network and cloud-native controls to enforce segmentation and minimize blast radius.
Integration is the key challenge here. Tools in silos don’t add up to preemptive defense. ReliaQuest GreyMatter solves this by being technology-agnostic - stitching together telemetry from across your stack to provide a single, unified picture of risk and the automated workflows to act on it.
Ready to see how GreyMatter Discover integrates seamlessly into your existing stack?