Investigation automation is the application of artificial intelligence (AI), machine learning (ML), and automated response playbooks to gather evidence, correlate signals, enrich data, detect attack patterns, and suggest or even take autonomous action.
Investigation automation turns raw data into actionable intelligence without having to manually search logs or pivot between tools.
In modern security operation centers (SOCs), analysts can encounter tens of thousands of alerts every day. Legacy tools are no longer effective in handling this scale. Here, investigation automation fills the gap between the volume of alerts and the analyst’s capacity to process them, making it possible to resolve incidents at machine speed.
Why Investigation Automation Is Critical to Outpace Threats
1. Attackers Move in Minutes
Data breaches now happen faster than security teams can react to them. Advanced threats (like ransomware, supply chain attacks, or lateral movement attacks) can spread across a network in minutes. Human teams cannot investigate them that quickly without adopting automation.
Automated incident investigation solutions can examine millions of logs in seconds, detect anomalies, and respond to high-risk alerts with up to 99.4% accuracy before damage escalates.
2. Analysts Are Drowning in Noise
SOCs have to handle floods of alerts: tens of thousands every day. Alert fatigue, combined with the need to perform mundane, repetitive tasks, can lead to errors and threats slipping through the nets.
Automation of the investigation process means that even low-priority or high-volume alerts are treated equally. AI-driven investigation platforms eliminate false positives, connect related indicators, and point out key findings, making it easier for analysts to make strategic decisions.
3. AI Makes Investigations Dynamic, Visual, and Context-Aware
Static dashboards and tables don’t cut it anymore. New generative user interfaces (UIs) offer visual, context-driven investigative processes.
Dynamic investigation environments can automatically summarize evidence, point out anomalies, and display findings in adaptive visual cards. Analysts can engage with incident timelines, asset maps, and behavior patterns, which helps them to better understand intricate attacks in a few minutes instead of hours.
What Investigation Automation Typically Includes
Automation of investigation involves various levels and functionalities of detection, triage, and remediation. Contemporary SOC solutions integrate AI, machine learning, and workflow automation to provide meaningful incident storytelling from raw alerts. The key components include:
Automatic Evidence Gathering: This involves the continuous collection of logs, endpoint data, network activity, cloud events, and identity activity. This ensures that no important information is left out, even in hybrid and multi-cloud environments, and minimizes the time spent by analysts in manually gathering information.
Contextual Enrichment: Raw alerts are then enriched with threat intelligence, value to assets, identity information, and historical information. This provides a complete view of each incident, and analysts can easily assess the severity of the incident.
Event Correlation Across Tools: Notifications from SIEM, XDR, EDR, network monitoring, and identity platforms are automatically correlated to provide a complete story of the incidents. This reduces the need for manual processes across different tools.
Dynamic Visualizations and Guided Narratives: Investigations are represented through interactive timelines, graphs, and visual narratives. The analysts are able to visualize the flow of events, affected systems, and lateral movement possibilities.
Automated Root-Cause Analysis: The AI system pinpoints the initial compromise, lateral movement, and attack chain. This helps in rapid mitigation and strategic planning to avoid future occurrences.
Risk Scoring and Prioritization: Incidents are scored based on business impact, exploitability, and asset value. High-risk threats are prioritized for immediate attention, ensuring that analysts work on the most operationally and financially risky incidents.
Automated Containment Actions: Platforms are capable of performing predefined or AI-driven actions, such as terminating malicious processes, segregating infected hosts, or revoking compromised credentials.
Collectively, these features make possible end-to-end investigation workflows. Fragmented alerts are turned into meaningful investigations, enabling analysts to respond to incidents quickly and accurately while dedicating time to strategic threat hunting and proactive security operations.
The Benefits of Investigation Automation
The automation of investigations translates to tangible value in terms of speed, accuracy, and analyst productivity. In the case of large enterprise SOCs that are dealing with a large number of alerts and complex environments, the value of automation goes beyond mere efficiency gains.
Massive Drop in Investigation Time
Evidence collection and correlation by AI significantly cut down the mean time to investigate (MTTI). As a result, analysts spend less time searching for information and more time analyzing results and making strategic decisions.
Increased Accuracy of Detection with ML
Machine learning algorithms detect anomalies and threats that may not be visible to human analysts. With continuous learning from past events, AI-powered investigation optimizes detection accuracy over time.
Reduced Mental Load on Analysts
AI-powered investigation filters noise and helps analysts focus on difficult investigations.
Less Human Error
Human pivoting, copying logs, or lack of context can introduce errors. Automation eliminates the possibility of human error in evidence collection, scoring, and correlation.
Improved Visibility and Decision-Making
Automation of investigations offers a single pane of glass for alerts, assets, and attack chains, providing decision-makers with complete context to make faster decisions.
Earlier Detection of Lateral Movement and Stealthy Attacks
Continuous automated monitoring helps in the detection of subtle attack indicators, lateral movement, privilege escalation, or stealthy exfiltration before damage is done.
With today’s platforms, automation is now capable of handling investigations from the time of detection through triage and root cause analysis to containment, making it an end-to-end process.
Market Trends and Research Insights
The automation of investigations did not happen in a vacuum. It is at the heart of changes in security operations, artificial intelligence, and risk management. As unscrupulous actors scale faster and environments get more complex, the industry is firmly on the move towards intelligent, adaptive, and integrated investigation solutions. The following trends demonstrate how the modern SOC is reshaping what efficient investigation means:
From Dashboards to Generative Interfaces: Research is shifting from static dashboards to adaptive and generative interfaces that emphasize patterns, hypothesis development, and analysis.
AI-Driven Automation: Next-generation platforms use ML, AI reasoning, and orchestration to perform full lifecycle investigation and response without human intervention.
Convergence of Threat Hunting and Investigation: Automated processes are now used for evidence gathering, enrichment, scoring, and correlation, allowing analysts to concentrate on advanced threat hunting.
Transition from Reactive to Proactive Models: Organizations embracing automated investigation capabilities are able to identify early signs of compromise and act before attacks mature.
Integration with CTEM, SOAR, and SIEM: Integrating CTEM, SOAR, and SIEM enables automated processes to work end-to-end on the attack surface.
Organizations that automate threat investigation capabilities can have up to 100% of alerts investigated by AI with over 99% investigation accuracy.
Examples of Automated Investigation Workflows
Modern investigation happens through structured, repeatable workflows that proceed from alert to answer with minimal human intervention. Rather than forcing analysts to context-switch between tools, manually collect logs, and correlate events, automated investigation platforms run predefined and AI-driven workflows in the background. These workflows automatically gather evidence, build context, calculate risk scores, and identify clear paths forward.
This enables faster time-to-answer, improved consistency of investigation outcomes, and reduced analyst cognitive burden across the SOC. The following examples demonstrate how automated incident investigation happens in practical enterprise settings.
For instance:
Malware Alert Triage:
Automated evidence collection, including gathering of endpoint logs, process information, and network traffic.
ML-based scoring of artifacts to identify files as malicious, suspicious, or harmless.
Automated enrichment with threat intelligence feeds.
Dynamic visual storytelling of affected hosts and possible lateral movement.
Phishing Investigation:
Identify and investigate phishing threats with AI-driven precision.
Automated domain analysis for spoofing detection.
Root-cause analysis to determine affected accounts and points of entry.
Automated containment: password reset, MFA enforcement, and mailbox quarantine.
Insider Threat Detection:
Continuous monitoring of file access, login activity, and privileged access.
AI-driven detection of anomalies and unusual behavior patterns.
Evidence scoring in context with past incidents.
Dynamic alerts and recommended actions for analysts.
These processes demonstrate how security automation of investigations can speed up response, enhance accuracy, and decrease the workload of analysts.
Emerging AI Capabilities in SOC Investigations
Contemporary SOCs are quickly embracing the use of AI-based technologies to improve their response processes, gain accuracy, and streamline investigations. Some of the most promising new capabilities include:
Agentic AI: Agentic AI is different from traditional AI tools, which need constant human interaction to function. Agentic AI is self-sufficient and can independently carry out investigative tasks. It can analyze and correlate evidence, send alerts, find vulnerabilities, and even suggest or implement remediation actions without needing human input, allowing continuous 24/7 investigation.
Predictive Threat Modeling: Based on past attack behavior, system dynamics, and environmental factors, predictive modeling uses the knowledge of probable attack vectors and targets to predict potential attacks. This allows SOC analysts to anticipate potential threats to high-risk systems and take proactive measures to neutralize them before they become serious threats.
Dynamic Evidence Correlation: AI tools are capable of correlating logs, alerts, endpoint, and network data from various sources into meaningful incident stories. This makes it easier to identify connections between events and reveal complex attack patterns that could have been overlooked.
Generative UI for Investigations: Interactive and AI-powered dashboards enable analysts to work with dynamic visualizations, hypothesis suggestions, and timelines. These tools enable investigators to navigate incidents, detect anomalies, and make informed decisions with reduced mental overhead.
Automated Triaging and Enrichment: AI systems are capable of automatically prioritizing alerts, pointing to the most important findings, and enriching unrefined data with threat intelligence in real-time. This ensures that analysts are working with signals and not noise.
This year, AI investigation tools will be essential for large-scale enterprises operating in complex hybrid environments and handling high volumes of security alerts. Enterprises that leverage agentic AI, predictive modeling, and automated enrichment will not only be able to respond faster but also improve the accuracy of detection and remain resilient against sophisticated cyber threats.
How Modern Tools Reduce Noise and Cognitive Load
Contemporary SOC solutions use automation to:
Filter Thousands of Security Alerts Daily: Automation tools help distinguish between relevant and irrelevant alerts, ensuring that analysts are only alerted to relevant incidents and not drowned in low-priority alerts.
Overlapping Artifacts Consolidation: Duplicates in logs, alerts, or telemetry data can lead to confusion and unnecessary work. Automated evidence correlation helps to consolidate such data into a single, meaningful piece of evidence, eliminating the need for repetitive investigations.
High-Risk Alert Prioritization: AI-powered scoring helps to prioritize alerts based on business risk, exploitability, and value of assets, ensuring that analysts are alerted to incidents that are of highest concern to the business.
Creation of Visual Timelines and Storyboards: Difficult incidents are broken down into easy-to-understand visual representations, illustrating the sequence of events, involved systems, and possible lateral movement.
Offer Recommended Next Steps and Automated Remediation: Analysts are provided with recommendations or automated responses for containment, ensuring rapid and consistent remediation.
With the integration of AI, machine learning, and workflow orchestration, contemporary investigation platforms have lightened the cognitive load. Analysts no longer need to manually trawl through and analyze swathes of alerts, combine multiple data sources, or mentally try to reconstruct attack paths.
This lessens the chances of mistakes, quickens decision-making, and enables SOC teams to concentrate on high-value activities such as proactive threat hunting, hypothesis validation, and strategy formulation. Over time, organizations will enjoy faster incident response times, enhanced accuracy, and a stronger security posture.
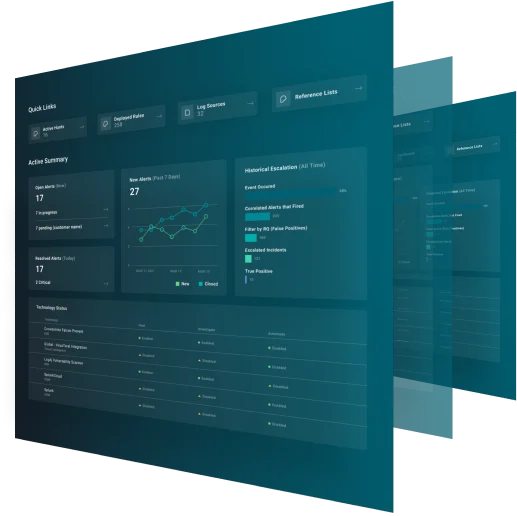
How ReliaQuest Automates Investigation
ReliaQuest GreyMatter is an agentic AI security operations platform that integrates into the fabric of enterprise SOCs—across every tool, environment, and entity— to give security teams the speed to break free from reactive operations, the capabilities to scale proactive programs, and the foresight to become predictive so they stay ahead of adversaries and advise the business faster.
GreyMatter offers AI-driven investigation for the enterprise SOC. The agentic AI security operations platform automatically:
Correlates Multi-Source Telemetry: GreyMatter combines alerts and telemetry data from endpoints, networks, cloud infrastructure, and identity infrastructure into a single, unified view. By automatically connecting related events from disparate sources, it gives analysts a complete picture of an incident, removing the need for manual cross-platform analysis and revealing hidden attack chains.
Enriches Detections With Threat Intelligence: Every detection is enriched with context, including threat actor information, tactics, techniques, and procedures (TTPs), and attack patterns. It also queries CMDBs, asset/identity sources of truth, vulnerability scanners, historical incident data, performs OSINT lookups, and executes pivot plays based on observed patterns.
Reduces Complex Alert Processing: Cyber Analysis Methodology (CAM) is GreyMatter’s investigation methodology—the proprietary framework that enables comprehensive investigation at machine speed, including systematic data gathering, artifact extraction, enrichment, correlation, pivot plays, and verdict formation.
Produces Investigative Timelines: GreyMatter builds graphical incident stories that depict event order, lateral activity, and escalation routes. Interactive timelines enable analysts to investigate incidents in an intuitive manner, identify root cause events, and quickly assess the extent of a breach.
Identifies Root Cause and Lateral Activity: GreyMatter is able to automatically track back incidents to their root cause, pointing to compromised accounts, computers, or systems. Through the representation of lateral activity and escalation, analysts are able to gain valuable insights into the lateral movement of the attack.
Automates Recommended and Fully Executed Responses: GreyMatter’s automatically execute response actions such as isolating hosts, terminating malicious processes, or revoking compromised credentials. This enables the reduction of dwell time, limiting the potential scope of the attack, and ensuring successful response actions within the environment.
Operates as an Agentic AI System: Autonomous investigation and response are performed without requiring continuous human supervision, while security teams maintain full visibility into every AI investigation and can provide feedback directly in the platform. The architecture behind GreyMatter’s AI is an agentic AI system that shares agents, tools, memory, context, and capabilities. GreyMatter orchestrates these components to process natural language requests within a multi-system approach that enables agentic personas, including investigation and response, to achieve objectives end-to-end.
Agentic Memory Learns Continuously: GreyMatter’s agentic memory is a dynamic knowledge hub that retains customer-specific context, preferences, and historical feedback to deliver tailored and accurate investigation outputs.
Through the integration of automated investigation, ReliaQuest enables security teams to shift from reactive process to a proactive, continuous operation. Analysts are freed to focus on strategy and advanced threat hunting while the platform executes high-volume, repetitive tasks.
FAQs
What Is Investigation Automation?
Investigation automation is the application of AI, ML, and workflow engines to gather evidence, enrich and correlate security alerts, and suggest or perform response actions. It enables the translation of raw alerts into understandable incident stories and the performance of near real-time investigations.
How Does Automation Enhance Investigative Speed and Accuracy?
Automated processes minimize manual evidence gathering, enable the correlation of evidence from various sources, and apply AI to identify patterns that may not be observable to humans. This improves the accuracy of the time-to-answer.
What Are Examples of Automated Investigation Processes?
These include malware alert analysis, phishing investigations, and insider threat analysis, where evidence is automatically gathered, scored, correlated, and displayed as visual timelines for rapid analyst analysis.
What Kinds of AI Capabilities Are Emerging in SOC Investigations?
The key capabilities are agentic AI, predictive threat modeling, automated triage and enrichment, dynamic evidence correlation, and generative UIs that walk investigators through the process of an investigation.
How Do Modern Tools Mitigate Noise and Cognitive Overload?
They filter alerts, highlight high-risk or suspicious activity, combine redundant artifacts, display attack chains, and automate recommended actions, so investigators can concentrate on difficult decisions.
How Does ReliaQuest Automate Investigations?
ReliaQuest GreyMatter enables security teams with multi-source telemetry, enriches alerts with threat intelligence, builds investigative timelines, finds root cause and lateral movement, and automatically contains the threat. Its agentic AI teammates work continuously on investigations without human prodding.
What Are Typical Use Cases for Investigation Automation?
Investigation automation enables essential SOC use cases like malware analysis, phishing analysis, insider threat analysis, credential compromise analysis, and cloud security incidents. It is also employed for lateral movement analysis and multi-stage attack investigations in hybrid environments.
How Do Playbooks Relate to Investigation Automation?
Playbooks are pre-built workflows that are used to automate incident investigations and responses. Playbooks can initiate evidence collection, enrichment, scoring, and containment tasks depending on the alert type or risk level. More advanced AI-based investigation solutions can leverage playbooks with dynamic reasoning, which enables workflows to be context-aware and scalable.