Threat intelligence platforms (TIPs) collect, analyze, and disseminate information about cyber threats to help organizations improve their security posture. However, the process often stops at alert enrichment—leaving security teams with more dashboards, not more protection. TIPs rarely drive real-time responses or integrate intelligence into daily operations.
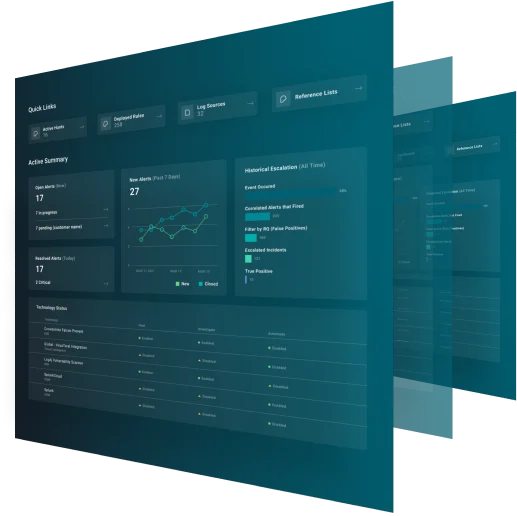
GreyMatter transforms threat intelligence into action. As an agentic AI security operations platform, GreyMatter ingests, contextualizes, and operationalizes threat data—enabling predictive detection, automated response, and measurable outcomes across your environment.
Breaking Down the Difference
See what sets ReliaQuest GreyMatter apart from Threat Intelligence platforms.
Capability | ReliaQuest GreyMatter | Threat Intelligence |
|---|---|---|
Goal | To improve security posture by collecting and analyzing data across your environment and automatically enriching alerts. | To improve security posture by collecting and analyzing data across your environment and automatically enriching alerts. |
Architecture | Leverages agentic AI to automate investigations and trigger response actions across your entire security stack, from any vendor, anywhere. | Limited to data collection, correlation, and aggregation. Not built take action—incapable of containing, responding, or investigating threats. |
Detection | Detects threats across any technology or vendor in your technology stack, leveraging API capabilities. | Relies on static feeds; detection is siloed in other tools. |
Containment and Response | Contains threats in under 5 minutes using automated workflows that orchestrate actions across your existing security stack. | No containment or response capability; teams must act manually, giving attackers more time to exploit vulnerabilities. |
Investigation | Agentic AI autonomously conducts full investigations from alert triage to executing response actions. | Limited to threat intelligence enrichment only; investigations are slow and manual. |
Integrations | GreyMatter has 250+ pre-built integrations and leverages the universal translator to normalize data across disparate technologies. | Limited integration with existing security tools, often requiring significant customization and advanced skills. |
Visibility | Provides detailed telemetry data across endpoints, networks, cloud environments, and applications. Captures and analyzes the data needed to respond to threats effectively. | Primarily focuses on aggregating threat feeds from external sources and providing threat dashboards. Lacks integration with internal telemetry, making it harder to contextualize threats against your assets and exposures. |