Editor’s note: This report was authored by Joseph Keyes and Daxton Wirth.
Key Points
Ransomware operator “LeakNet” has added “ClickFix” lures delivered through compromised legitimate websites as a newly confirmed initial access method.
In addition, a previously unreported Deno runtime loader executes a base-64 encoded payload almost entirely in memory, fingerprints the victim machine, and establishes a command-and-control (C2) connection.
In every confirmed LeakNet incident, we observed the same post-exploitation chain:
jli.dllside-loading into Java in theUSOShareddirectory, PsExec-based lateral movement, and S3 bucket payload staging.Defending against LeakNet means hardening at multiple layers: Block newly registered domains, restrict Win-R access, and limit PsExec to authorized administrators.
Ransomware operator “LeakNet” is currently averaging about three victims per month, but it’s scaling up and shifting tactics. In recent incidents we investigated, the group added a new initial access path and a new loader technique: “ClickFix” lures hosted on compromised websites and a Deno-based, in-memory loader that most security tools won’t catch. No matter how it gets in, LeakNet then follows the same post-exploitation steps: execution, lateral movement, and payload staging.
Two developments stand out. First, we assess with high confidence that LeakNet is using ClickFix (a social engineering technique that tricks users into manually running malicious commands via fake error prompts) delivered through legitimate websites that have been compromised. This seems to be a move away from relying on initial access brokers (IABs) for stolen credentials (which was likely the group’s previous tactic) and toward running its own campaigns directly. Second, ReliaQuest identified a staged command-and-control (C2) loader built on Deno (a JavaScript/TypeScript runtime similar to Node.js) that executes payloads primarily in memory.
The key takeaway here is that both entry paths lead to the same repeatable post-exploitation sequence every time. That gives defenders something concrete to work with: known behaviors you can detect and disrupt at each stage, well before ransomware deployment, regardless of how LeakNet got in.
In this spotlight, we:
Break down LeakNet’s expanded initial access methods, including ClickFix hosted on compromised legitimate websites and a novel Deno-based, in-memory loader.
Explain how a consistent post-exploitation playbook—
jli.dllside-loading, PsExec lateral movement, and S3 bucket staging—creates a repeatable and detectable attack chain.Detail how LeakNet is compressing the path from initial access to encryption, with actionable guidance to detect, contain, and get ahead of these intrusion paths before ransomware deploys.
LeakNet Levels Up with ClickFix and Deno
The sections below detail two developments that are expanding LeakNet's reach: a shift to ClickFix lures for self-directed initial access and a Deno-based C2 loader that executes payloads in memory while leaving minimal forensic traces. Together, they represent a group investing in its own infrastructure and evasion capabilities.
ClickFix Gives LeakNet a New Front Door
On top of purchasing access from IABs, LeakNet now seems to be running its own ClickFix campaigns to reach victims directly. Where LeakNet previously relied largely on pre-built footholds from IABs and compromising edge devices, it’s now generating its own entry points with ClickFix. That creates a gap for defenders: Dark-web monitoring for IAB activity no longer captures the full picture of how LeakNet is sourcing access, which puts more weight on detecting suspicious behavior after a user takes the bait. This shift reduces LeakNet’s dependence on third-party suppliers, lowers its per-victim acquisition cost, and removes the operational bottleneck of waiting for valuable accounts to hit the market. It also expands the pool of potential victims, as LeakNet is no longer limited to another threat actor’s target list.
In several recent incidents, ReliaQuest attributed the activity to LeakNet with high confidence based on overlapping infrastructure and tactics, techniques, and procedures (TTPs) consistent with previously confirmed LeakNet behavior. The group delivered a ClickFix lure (see Figure 1) through a compromised legitimate website that prompted the user to run an msiexec command. That command downloaded and executed LeakNet’s loader.
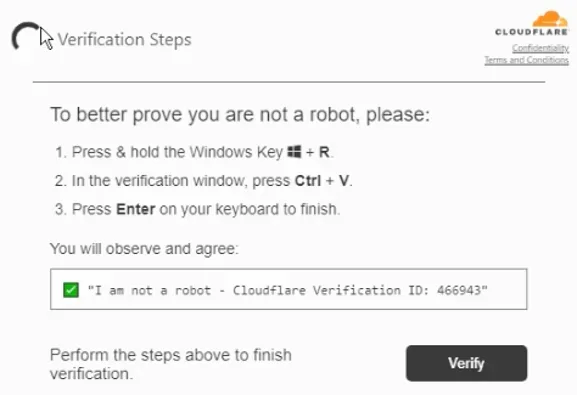
Figure 1: ClickFix lure that incorporates a fake Cloudflare Turnstile verification page
|
By utilizing ClickFix, any employee who browses the web could become an entry point. LeakNet’s ClickFix campaign doesn’t target specific users or companies. Instead, the group casts a wide net and relies on volume, working on the assumption that a proportion of users who encounter the lure will execute the malicious command. In the incidents ReliaQuest analyzed, users were compromised through ordinary web browsing, consistent with opportunistic delivery. That means there’s no “target profile” to match against and no advance warning that an organization is in scope.
LeakNet isn’t alone in using ClickFix for initial access. The technique has grown quickly: ClickFix facilitated the delivery of 59% of the top malware families tracked in 2025, and more threat groups are adopting it to drive user execution and deliver follow-on payloads.
LeakNet’s adoption of ClickFix marks both the first documented expansion of the group’s initial access capability and a meaningful strategic shift. By moving away from IABs, LeakNet removes a dependency that naturally constrained how quickly and broadly it could operate. And because ClickFix is delivered through legitimate—but compromised—websites, it doesn’t present the same obvious signals at the network layer as attacker-owned infrastructure (for example, newly registered domains). The signal shows up only after the command is executed. Detection should focus on what follows the user action: suspicious msiexec commands, unexpected outbound connections to external staging infrastructure, and commands that are unusual for that user.
LeakNet Adds a Stealthy Deno-Based Loader
LeakNet isn’t just changing how it gets in with ClickFix. Across multiple intrusion attempts, we saw the same loader behavior show up repeatedly, suggesting the group is expanding its execution options.
ReliaQuest has high confidence that LeakNet is using a Deno-based loader that executes base64-encoded JavaScript directly in memory. That leaves minimal on-disk evidence and helps the activity blend in with a legitimate developer tool. It’s an effective follow-up to ClickFix: Once a user runs the initial command, LeakNet can move quickly into a quieter second stage that many file-based controls may miss. Defenders should focus on behavioral and command-line-based detection and treat tools like Deno as dual-use execution surfaces, not automatically “safe” developer utilities.
Deno is a legitimate runtime developers use to execute JavaScript and TypeScript. LeakNet abuses that legitimacy with a “bring your own runtime” (BYOR) approach. Rather than deploying a custom malware loader that’s more likely to get flagged, the attackers install the legitimate Deno executable and use it to run malicious code. In observed activity, that process was initiated through Visual Basic Script (VBS) and PowerShell scripts, cleverly named Romeo*.ps1 and Juliet*.vbs.
The key advantage is delivery. Instead of writing a malicious JavaScript file to disk, LeakNet passes the code to Deno as a base64-encoded data: URL. Deno then decodes and executes it directly in memory. In practice, that means the script never appears as a normal file on the endpoint, reducing forensic artifacts and making the activity look more like a one-off developer task than a traditional C2 loader.
|
Once running, the payload:
Performs basic host fingerprinting by collecting the username, hostname, total system memory, and operating system (OS) release
Hashes the data to create a unique victim identifier
Checks in to attacker-controlled infrastructure to select a C2 endpoint and request a victim-specific second-stage payload
Attempts to bind to a local port (likely to prevent multiple instances from running simultaneously)
Enters a polling loop that repeatedly fetches and executes additional code through Deno
This approach has two immediate consequences for defenders:
File-scanning and signature-based endpoint controls may generate little to no signal when there’s no conventional payload written to disk.
Allowlists and “unknown binary” heuristics are less effective because Deno is legitimate and signed.
The suspicious part isn’t Deno’s presence—it’s what’s happening inside it, i.e., unusual command-line arguments, network activity, and in-memory execution patterns. This means traditional file-based detections may miss the activity, so defenders must prioritize behavioral signals such as Deno running outside development environments, suspicious parent-child process chains, and unexpected outbound connections.
The Same Loader, a Different Door
ReliaQuest also observed a separate intrusion attempt in which threat actors used Microsoft Teams phishing to socially engineer a user into launching a payload chain that ended in a similar Deno-based loader. Although the initial access vector differed from LeakNet's confirmed delivery methods, the activity was similar: The user was prompted to download and run a Microsoft Installer (MSI) and a VBS file, which then executed a base64-encoded Deno loader consistent with the same BYOR pattern.
That activity was remediated quickly, so attribution remains inconclusive. But the overlap is still meaningful. Either LeakNet is expanding its initial access channels, or other actors are starting to use this Deno-loader technique.
Inside LeakNet’s Post-Exploitation Playbook
Operational consistency is an advantage for defenders. LeakNet uses the same post-exploitation techniques regardless of how it gets initial access. That matters because it makes the group’s behavior predictable—and if you recognize the sequence, you can disrupt it even when the entry point changes.
The chain typically starts with Dynamic Link Library (DLL) sideloading, a technique where a malicious DLL file is placed next to a trusted program so that Windows loads it first. LeakNet uses a legitimate Java process as the carrier and drops the malicious jli.dll file in the directory “C:\ProgramData\USOShared” which is associated with Windows Update related activity. To the system—and often defenders at first glance—it’s just a legitimate process running from a familiar location.
After execution, activity shifts to C2, with beaconing (regular outbound check-ins to a C2 server) observed to multiple domains across different incidents but following the same general URL structure (see below), which creates a reliable opportunity for static detection.
|
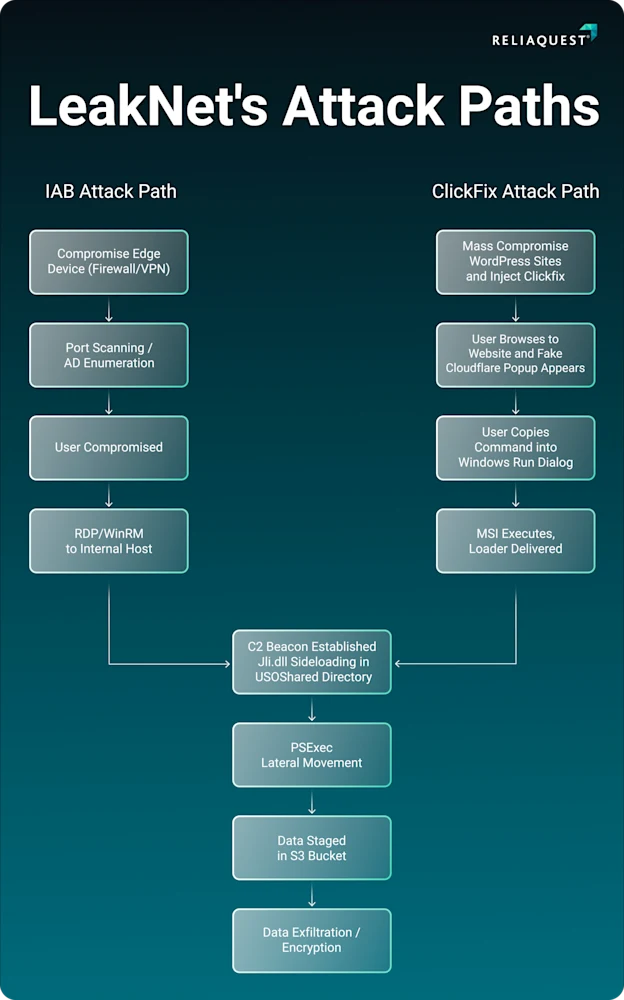
Figure 2: ClickFix lure that incorporates a fake Cloudflare Turnstile verification page
Next comes lateral movement with PsExec, a legitimate Windows administration tool. Before moving, LeakNet runs cmd.exe /c klist, a built-in Windows command that displays active authentication credentials on the compromised system. This tells the attacker which accounts and services are already reachable without the need for requesting new credentials, so they can move faster and more deliberately. For staging and exfiltration, LeakNet uses S3 buckets, exploiting the appearance of normal cloud traffic to reduce its detection footprint.
Each technique borrows legitimacy from something defenders expect to see: a recognized runtime, a standard admin tool, a common cloud service. That’s how LeakNet stays under the threshold of many standard controls.
The flip side is that LeakNet's consistency is also its biggest weakness. Because the same tools and techniques show up across every incident, a handful of well-placed behavioral detections can cover the entire known attack surface. Prioritize:
Unusual DLL sideloading behavior in non-standard directories
Anomalous PsExec usage that doesn’t match expected administrative patterns
Unexpected outbound connections to S3 buckets from systems
When these signals appear together, the window to act is narrow. Isolating the affected host at the first confirmed post-exploitation indicator is often the best chance to disrupt the chain before it runs to completion.
Step Up Your Defenses Against LeakNet-Style Intrusions
ReliaQuest GreyMatter gives your team practical ways to quickly detect, contain, investigate, and remediate the TTPs outlined in this report, including:
Agentic AI: Traditional signature-based defenses are strong at catching known malicious files but they can miss LeakNet's abuse of legitimate binaries (like Deno) and trusted system directories like USOShared. Agentic AI focuses on behavior, such as Deno executing outside of a designated development environment, java.exe loading jli.dll from C:\ProgramData\USOShared, msiexec commands spawned from browser processes, or an in-memory payload establishing a persistent outbound loop to an attacker-controlled C2 server without writing anything to disk.
GreyMatter Transit: LeakNet's Deno loader establishes C2 immediately after fingerprinting the victim machine, and the group uses S3 buckets to stage additional payloads in a way that blends with legitimate cloud traffic. GreyMatter Transit provides visibility into data as it moves across the network, allowing for real-time detection of anomalous outbound connections from unexpected processes, repeated beaconing patterns consistent with LeakNet's C2 loop, and lateral movement traffic associated with PsExec propagation—even when disguised as routine administrative or cloud activity.
GreyMatter Digital Risk Protection: GreyMatter Digital Risk Protection (DRP) monitors dark-web forums, criminal marketplaces, and underground communications for references to your organization, leaked credentials, and chatter about ClickFix campaigns or tooling associated with LeakNet's known infrastructure. This provides early warning to harden defenses and close exposure before a lure reaches your users.
Detection Rules: ReliaQuest's detection rules are continuously updated using the latest relevant threat intelligence and research, allowing organizations to defend against LeakNet's evolving techniques, including fileless execution methods, like the Deno loader, that have minimal prior public coverage and no existing signatures in most environments.
Organizations can reduce their mean time to contain (MTTC) threats from hours to just minutes and minimize the risk of ransomware deployment by deploying these rules alongside these GreyMatter Automated Response Playbooks:
Isolate Host: Quarantines compromised systems at the first confirmed sign of post-exploitation activity, including
jli.dllside-loading events or anomalous PsExec usage, halting LeakNet's lateral movement before it can reach additional hosts or progress to encryption.Block Domain: Severs communication with LeakNet's attacker-controlled C2 servers and S3 staging infrastructure, disrupting the persistent beaconing loop established by the Deno loader and preventing additional payload retrieval critical to the group's attack chain.
Ban Hash: Prevents execution of known malicious components across the environment. Banning file hashes associated with trojanized
jli.dllvariants and malicious MSI packages stops LeakNet's payloads from executing on additional hosts, cutting off both spread and persistence before the post-exploitation playbook can run to completion.
Your Action Plan
LeakNet is shortening the path from initial access to lateral movement by relying less on IABs and running its own ClickFix lures. The actions below focus on preventing initial access and lateral movement associated with LeakNet.
Block Newly Registered Domains: C2 domains spun up associated with this campaign are usually only a few weeks old. Newly registered domains are rarely needed for business operations and have a big effect on making it harder for threat actors to spin up new infrastructure.
Block users from using Win-R: Regular non-technical users should not have access to run Win-R on their Windows Workstation.
Prevent PSExec from unauthorized users: Regular non-technical users should not have access to run PsExec. Create a Group Policy Object (GPO) to block its use to only allow authorized admins.
Key Takeaways and What’s Next
LeakNet is at an inflection point, and the window to get ahead of what comes next is now. The move to self-directed ClickFix delivery, the introduction of a fileless in-memory loader, and a post-exploitation playbook that’s already proven successful across incidents aren’t isolated changes. They’re the building blocks of a group removing constraints on how quickly and broadly it can operate. LeakNet is expected to continue to ramp up, and early detection of the tradecraft in this report is the clearest opportunity to disrupt that trajectory.
Looking ahead, this likely won’t stay contained to LeakNet. Fileless execution techniques that effectively evade traditional controls tend to spread, and the Deno loader is likely to draw attention from other threat actors as its effectiveness becomes more visible. ClickFix delivery is already spreading, accounting for the delivery of 59% of the top malware families tracked in 2025. If detection coverage around jli.dll and PsExec improves, it would be consistent for LeakNet—or similar ransomware groups—to rotate to alternate sideloading targets or additional living-off-the-land binaries (LOLBins) as those specific techniques become easier to catch.
To stay ahead, shift detection focus away from the delivery layer and toward the behavioral signals that follow. Visibility into anomalies such as Deno running outside development environments, jli.dll side-loading in unexpected locations, and unusual PsExec usage is likely to offer the most reliable coverage against the techniques described in this report. Strong behavioral detections paired automated response capabilities built around these signals give security teams the best chance to intervene before the attack chain reaches encryption.
MITRE ATT&CK TTPs
Tactic ID | Tactics | Sub-technique ID: | Sub-technique: |
|---|---|---|---|
TA0001 | Initial Access | T1189 | Drive-by Compromise |
TA0002 | Execution | T1204.004 | User Execution: Malicious Copy and Paste |
TA0002 | Execution | T1059.007 | Command and Scripting Interpreter: JavaScript |
TA0005 | Defense Evasion | T1218.007 | System Binary Proxy Execution: msiexec |
TA0005 | Defense Evasion | T1574.001 | Hijack Execution Flow: DLL |
TA0005 | Defense Evasion | T1620 | Reflective Code Loading |
TA0008 | Lateral Movement | T1021.002 | Remote Services: SMB/Windows Admin Shares |
TA0011 | Command and Control | T1071.001 | Application Layer Protocol: Web Protocols |
TA0011 | Command and Control | T1102.002 | Web Service: Bidirectional Communication |
IOCs
Artifact | Details | Artifact | Details |
|---|---|---|---|
tools.usersway[.]net | Clickfix Domain on Compromised Websites | okobojirent[.]com | Deno C2 Domain |
apiclofront[.]com | Clickfix Domain | mshealthmetrics[.]com | Deno C2 Domain |
sendtokenscf[.]com | Clickfix Domain | verify-safeguard[.]top | Deno C2 Domain |
binclloudapp[.]com | Clickfix Domain | 194.31.223[.]42 | Deno C2 IP Address |
neremedysoft[.]com | Sideloaded jli.dll C2 Domain | 144.31.2[.]161 | Deno C2 IP Address |
ndibstersoft[.]com | Sideloaded jli.dll C2 Domain | 87.121.79[.]6 | Deno C2 IP Address |
windowallclean[.]com | Sideloaded jli.dll C2 Domain | 87.121.79[.]25 | Deno C2 IP Address |
cnoocim[.]com | Deno C2 Domain | 144.31.54[.]243 | Deno C2 IP Address |
delhedghogeggs[.]com | Deno C2 Domain | 144.31.224[.]98 | Deno C2 IP Address |
serialmenot[.]com | Deno C2 Domain | fastdlvrss.s3.us-east-1.amazonaws[.]com | Malicious S3 Bucket |
crahdhduf[.]com | Deno C2 Domain | backupdailyawss.s3.us-east-1.amazonaws[.]com | Malicious S3 Bucket |
weaplink[.]com | Deno C2 Domain |