Editor’s note: This report was authored by John Dilgen & Alexa Feminella
Key points
Former “Black Basta” affiliates are highly likely evolving the group’s social engineering playbook, using automated email bombing and Teams-based social engineering to gain remote access to senior-level employees within minutes.
77% of such incidents in March 2026 targeted leadership, up from 59% in the first two months of the year. Manufacturing and PSTS account for 26% of incidents each, consistent with Black Basta's historical targeting preferences.
Since the groups’ decline, 56% of all Teams-based phishing activity has occurred in 2026 alone. We assess with high confidence this is a unified campaign by former affiliates, not independent copycats.
Defenders must implement out-of-band verification for any help desk request involving remote access, enforce strict remote access tooling control, and run targeted simulations for senior personnel.
A new campaign is successfully evolving “Black Basta’s” signature social engineering playbook into a faster, more targeted, and increasingly automated intrusion method aimed at senior leadership.
Black Basta was a prolific Russia-linked ransomware-as-a-service (RaaS) group active from early 2022 until its internal chat logs were leaked in February 2025. This campaign, likely conducted by former affiliates, uses an automated, two-pronged social engineering attack: mass email bombing to overwhelm a target’s inbox followed by Microsoft Teams-based help desk impersonation to gain remote access. In some cases, attackers moved from initial chat engagement to executing malicious scripts in as little as 12 minutes.
56% of the Teams phishing activity we’ve observed since Black Basta’s decline in early 2025 occurred in the first four months of 2026 alone, with 32% happening in March. This begs the question: Why is the playbook of a now-defunct group surging, months after its collapse? Throughout this report, we will detail the indications that led us to conclude it’s highly likely a unified campaign from former affiliates who are carrying this tradecraft forward and evolving it by targeting senior leadership. From March 1 to April 1, 2026, 77% of observed incidents targeted senior-level employees, up from 59% in the first two months of 2026.
This activity demonstrates that a threat group’s most effective tactics can long outlive the group itself. Defenders should treat this as a signal to reassess help desk verification procedures, tighten controls around remote access tooling, and ensure detection logic accounts for evolving pretexts and tool rotation detailed in this report.
In this report, we:
Detail how attackers combine email bombing and Teams-based impersonation to target senior personnel.
Examine how Black Basta's tradecraft continues to shape current threat activity despite the group's public decline.
Assess targeting patterns, attribution signals, and defensive steps to disrupt similar intrusions.
Black Basta’s Playbook Lives On, Refined and Scaled
32% of the Teams phishing activity we’ve observed since May 2025 occurred in March 2026 alone. Across these intrusions, we identified three defining characteristics: a focus on senior leadership, automated attack timelines, and a rotating set of remote access tools. The following sections examine each in detail.
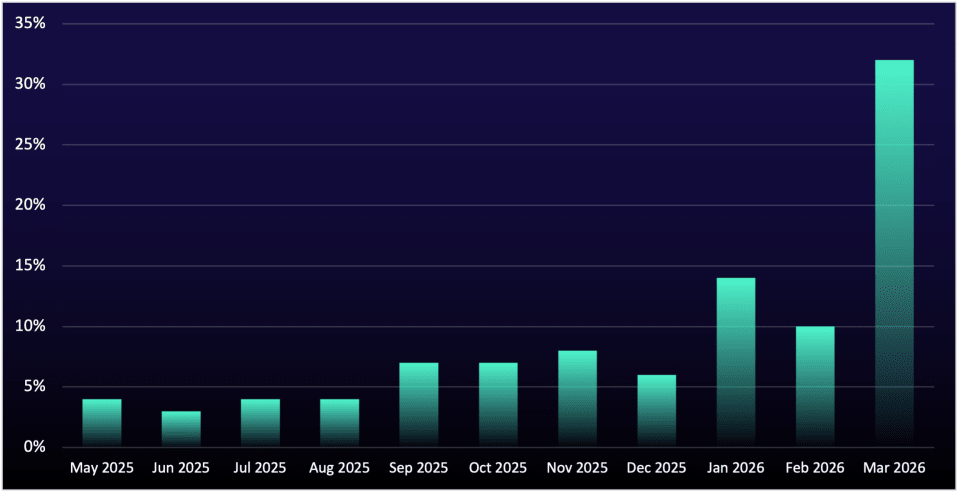
Figure 1: Monthly distribution of Teams phishing activity since May 2025, culminating in a surge in March 2026
Senior Personnel Targeted in Manufacturing and PSTS Sectors
This campaign's most significant evolution is its focus on targeting senior leadership, a tactic designed to secure high-privilege access from the very start and eliminate the need for noisy, time-consuming post-compromise escalation. In March 2026, 77% of attacks targeted executives, managers, and directors, up from 59% during January and February 2026.
That increase likely reflects a direct refinement to the attackers' automated targeting: During the earlier period, most of the non-senior users targeted held titles such as project manager, a role that superficially resembles management but carries far fewer privileges. The removal of such roles from targeting scripts appears to account for the jump, suggesting threat actors are likely actively iterating on their open-web reconnaissance automation to improve the quality of their target pool.
The strategic advantage is clear. An attacker who lands with high-level access from day one, a trend observed in 47% of all attacks ReliaQuest tracked in 2025, can move immediately to data theft or ransomware deployment, bypassing lateral movement and privilege escalation techniques (which are both time-consuming and create additional detection opportunities for defenders).
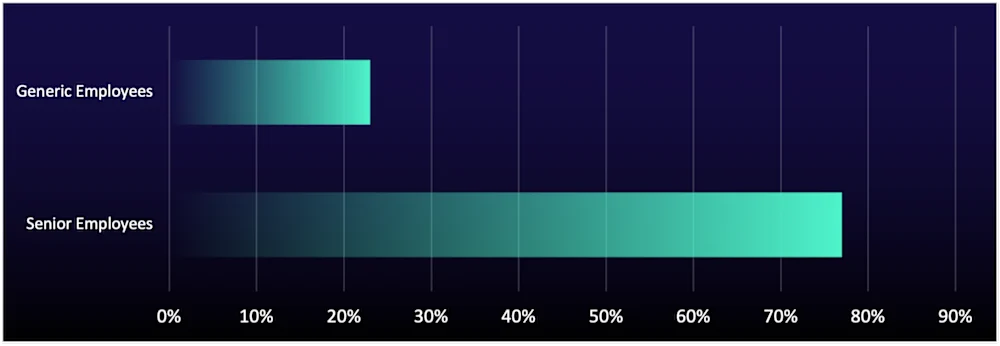
Figure 2: User targeting from recent Black Basta-style attacks
This risk is most acute in sectors where operational disruption carries immediate and severe consequences. Manufacturing and professional, Scientific, and Technical Services (PSTS) each accounted for 26% of all Black Basta-style incidents observed in 2026, and while all sectors were represented, this concentration indicates that the top two sectors were likely direct targets (see Figure 3). Both sectors tend to employ large, operationally pressured workforces that may be more susceptible to social engineering tactics such as vishing, and when the compromised user is a senior leader, the threat of ransomware halting production creates intense pressure to meet extortion demands quickly. This pattern closely mirrors Black Basta's known targeting preferences, as the group named more manufacturing organizations on its data-leak site than any other sector during its active period, further supporting the likelihood that former affiliates are behind this campaign. Organizations in both manufacturing and PSTS should expect this targeting to continue and intensify in the near term.
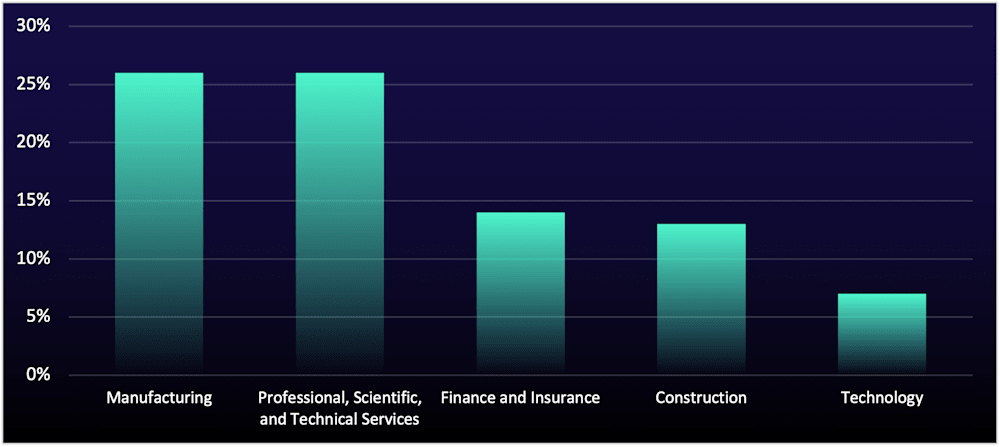
Figure 3: Top five sectors targeted in recent Black Basta-style attacks
Automated Social Engineering Enables Rapid Initial Access
Attackers are using automation to compress a multi-step social engineering attack into minutes, reducing the time defenders have to intervene before a live remote management session is established on a senior leader’s machine.
The initial access phase appears to follow a two-pronged approach that weaponizes a user’s own inbox to create urgency and make follow-on outreach appear credible. It begins with a high-volume email bomb (hundreds of emails sent in minutes) designed to overwhelm users and create confusion. Within minutes, the threat actor, posing as IT support, contacts the targeted user via a direct Microsoft Teams message or phone call to begin the next phase of the attack.
This follow-on activity also involves automation, or at minimum, a highly repeatable process. Chats directed at multiple users are often created within minutes of one another; in one instance, chats were initiated just 29 seconds apart. That pace is difficult to sustain consistently through purely manual targeting and suggests that the attackers are streamlining the early stages of engagement to reach users before defensive action can be taken.
Consistent with past Black Basta-style tradecraft, the campaign’s infrastructure shows a repeatable setup. The threat actors pose as internal support functions (e.g., “help desk”) and rely on consistent infrastructure elements across intrusions:
Russia-based source IP addresses to initiate contact (see IOC table for specific threat actor-linked IP addresses)
Disposable onmicrosoft[.]com tenant accounts, easily created and rotated to avoid blocklisting
Impersonation identities and chat names styled as internal IT or help desk personas to increase user trust
No single element here is unique, and the use of disposable Microsoft tenant accounts is now common across multiple threat groups. What distinguishes this campaign is the consistency with which these elements are combined and the speed with which the early engagement phase has been operationalized. Historically, social engineering attacks of this complexity often involved meaningful delay between steps, giving defenders time to detect and intervene. But now, the time between the first sign of an email bomb and an active remote session may be measured in minutes, and this automated playbook is being aimed squarely at an organization’s most privileged users. For defenders, email bomb activity should trigger immediate user notification and heightened scrutiny of any IT support outreach that follows.
A Preferred RMM Tool Surfaces Among Black Basta Affiliates
“Supremo Remote Desktop” has become a primary remote monitoring and management (RMM) tool in this campaign, allowing attackers to quickly turn social engineering into hands-on access to a victim’s host. This lightweight remote tool is legitimate but has malicious use cases, which makes it ideal for attackers to blend in with legitimate business activity. Security researchers have noted that Supremo was previously used by Black Basta affiliates in limited volume[i], which also supports the likelihood that the group's affiliates are behind this campaign. The tool's limited use also means that many defenders likely do not have security controls in place to prevent its execution and are less aware of its potential for malicious activity.
Once on the phone with the target user, threat actors convince them to join an RMM session, providing the attackers with control of the user's host. Through the RMM session, the attackers execute malicious scripts often named to resemble common email tools, such as MailAccountWizard.jar. By naming their scripts to mimic legitimate email utilities, the attackers reinforce their social engineering premise: that they are the help desk and are there to resolve the email bombing issue. While ReliaQuest has not observed ransomware deployment in the incidents described here, the techniques used are consistent with pre-ransomware staging, which suggests encryption will likely follow if attacks are successful (see Figure 4).

Figure 4: Pre-ransomware staging of Black Basta-style attacks
Supremo was not the only RMM tool recently observed; threat actors also used Quick Assist, which is natively installed on Windows 11 devices. To abuse this tool, target users are simply provided a hotkey, Windows Key + Control + Q, then given a code to enter. These are very easy instructions for non-technical users to execute, and Quick Assist requires no new software download; these two advantages make it more likely for the target user to join the remote session and less likely for defenders to notice an unauthorized RMM session, ultimately increasing the threat actor's chance of successfully deploying ransomware.
The use of RMM tools such as Quick Assist and Supremo is nothing new. In fact, Black Basta previously used Quick Assist extensively from 2024 to 2025. The reality that these tools are being leveraged again in 2026 highlights how difficult it is for organizations to close key foundational control gaps, such as help desk procedural flaws, and why attackers continue to exploit them. While many organizations may have restricted certain RMM tools through global policies or application controls, operational challenges such as new hosts joining the network through mergers and legitimate business requirements can leave persistent gaps. To reduce this exposure, defenders should regularly audit which RMM tools are permitted across their environments and enforce strict application controls.
Has Black Basta Returned?
This question matters because this activity reflects the reemergence of a highly effective intrusion model that has previously led to disruptive ransomware and extortion events. Even if actors are not operating under the Black Basta name, defenders are once again facing the same combination of email bombing, impersonated IT outreach, remote access abuse, and the now targeting high-value users.
This campaign closely matches historical Black Basta activity in its manufacturing sector targeting, use of specific but alternating RMM tools, and reliance on a well-established social engineering workflow. At the same time, some downstream elements do not point cleanly to Black Basta alone: Extortion activity has aligned at times with “Chaos” ransomware, while some tooling and naming conventions align with “FIN7.” These overlaps suggest not a neat attribution, but a fluid ecosystem in which operators and playbooks are reused across groups.
We see three plausible explanations:
Former Black Basta affiliates are regrouping under a new name;
Former affiliates are collaborating with another ransomware or extortion cluster; or
Another actor is adopting Black Basta-style tactics because they work.
Our assessment is that it is highly likely former Black Basta affiliates are involved, either regrouping or collaborating with others. Pure imitation is possible, but less likely given how closely the campaign aligns with legacy Black Basta tradecraft.
Ultimately, the "who" is less important than the "what." A proven, effective intrusion method is now more active and refined than ever, and organizations must be prepared to defend against the tactic, not just a name.
Step Up Your Defenses Against Black Basta-Style Intrusions
ReliaQuest’s Approach
This Black Basta-style campaign is built for speed, moving from an email bomb to a remote access session in minutes by exploiting human trust rather than technical flaws. ReliaQuest GreyMatter is designed to detect and respond to this behavioral chain by correlating weak signals across different technologies into a single, high-confidence alert.
GreyMatter Agentic AI focuses on the sequence of events rather than isolated alerts. An email bomb, a suspicious Teams chat from an external account, and the launch of an RMM tool are all low-fidelity events on their own. Correlated by GreyMatter, they describe the pattern of this campaign, allowing for detection before a malicious script is ever run.
ReliaQuest Detection Rules are continuously updated to surface the specific TTPs used in this campaign. By looking for behavioral indicators—like a massive influx of mail to one user, a Teams chat impersonating IT, or an RMM tool running from a user's downloads folder—we can identify the attack chain as it unfolds.
GreyMatter Automated Response Playbooks turn that detection into immediate action. Once the campaign is identified, pre-built playbooks can isolate the affected host, revoke the remote access session, and block the RMM tool's network communication—all within minutes and across your existing security stack. In a campaign designed to move from inbox to remote shell in under 10 minutes, automated containment removes the window attackers depend on.
Your Action Plan
This campaign moves at the speed of social engineering, meaning defenses must focus on disrupting the attack chain before remote access is achieved. These recommendations target the procedural and configuration gaps exploited by these actors:
Implement a Multi-Channel Verification Process for Help Desk Support: Do not rely on email or Teams chat alone to verify identity. Mandate a strict protocol in which any request for remote access requires out-of-band verification, such as a callback to the user's registered phone number or an approval flow through a separate, trusted application. This prevents an impersonator from controlling the entire communication channel.
Harden Controls Around RMM Tooling: Use application allow-listing to ensure only company-approved RMM tools can be executed, and restrict their use to authorized IT personnel only. For native tools like Quick Assist, use AppLocker or similar controls to prevent execution by general users, especially senior leaders who are less likely to need it. Block known malicious uses of RMM tools such as Supremo at the endpoint and network perimeter.
Conduct Targeted, Simulation-Based Training for Senior Personnel: General security awareness training is not enough. Run specific simulations for executives and managers that mimic this exact TTP: an email bomb, followed by an urgent Teams message from "IT support." The goal is to condition them to recognize that legitimate support will never create pressure or circumvent established verification protocols.
Key Takeaways and What’s Next
This campaign’s success reinforces what has been true for some time: Procedural gaps remain one of the most consistently exploitable weaknesses in enterprise environments. An attack chain that abuses employee trust in the help desk cannot be stopped by technology alone; it requires a strict, non-negotiable verification process for any request involving remote access. Given the low barrier to entry and high success rate, ReliaQuest assesses that within 12 months, a majority of social engineering–led initial access campaigns targeting enterprises will likely incorporate some variant of this help desk impersonation model.
As defenders adapt, attackers will too. As detections improve for common patterns like generic IT impersonation, repeated Teams outreach, or known RMM tools, expect pretexts to vary and tooling to rotate. The next likely RMM tool rotation may favor platforms that are pre-installed in enterprise environments (such as Remote Desktop or cloud-native tools) or tools with legitimate vendor presence that complicate allow-listing. Defenders should expect these intrusions to become more common, more tailored, and less reliant on static indicators over time.
Targeting is also likely to become more selective. Rather than broadly impersonating IT support to any senior employee, attackers are likely to narrow their focus to roles that provide the fastest path to monetization or operational disruption, such as CFOs and finance leaders, R&D leadership, plant or operations management, and other personnel with access to intellectual property, payment workflows, or production systems. In manufacturing especially, compromise of a single well-placed user could expose proprietary designs, supplier relationships, financial controls, or operational decision-making. As awareness improves across general leadership populations, threat actors will likely prioritize the users whose access creates the highest downstream leverage.
IOCs
Artifact | Details | Artifact | Details |
helpdesk[at]dpf.edu[.]lk | Email used for help desk impersonation | networksupport[at] techguard359. onmicrosoft[.]com | Email used for help desk impersonation |
Itsolution[at]helptech247. onmicrosoft[.]com | Email used for help desk impersonation | f51f2e98-9365-4666- 9be8-5b39063c6692 | Office 365 tenant used for help desk impersonation |
helpdesk[at]griffinintl[.]net | Email used for help desk impersonation | 2ad507a0-38a0-4574- baae-0ccc19c7e051 | Office 365 tenant used for help desk impersonation |
itdesk[at]itdesk[.]top | Email used for help desk impersonation | 84.42.94[.]127 | Threat actor-linked IP address |
it_assistance[at]teams000472. onmicrosoft[.]com | Email used for help desk impersonation | 84.42.92[.]225 | Threat actor-linked IP address |
h.tachouche[at] groupbiocare[.]com | Email used for help desk impersonation | 84.42.92[.]111 | Threat actor-linked IP address |
internalit[at]internalsupportteams. onmicrosoft[.]com | Email used for help desk impersonation | 84.42.92[.]176 | Threat actor-linked IP address |
[1] hxxps://github[.]com/BushidoUK/Ransomware-Tool-Matrix/blob/main/Tools/RMM-Tools.md