Editor’s note: This report was authored by Emily Jia
Key Points
In Q1 2026, ransomware pressure increased in two directions: established groups like “Akira” and “Qilin” maintained high victim volumes, while newer actors added noise and uncertainty.
“The Gentlemen” broke into the top tier, showing how quickly a capable group can scale. Meanwhile, “0APT” and “ALP-001” appeared to use questionable leak claims to pressure large enterprises.
Extortion group “ShinyHunters” showed that identity-first intrusions and software-as-a-service (SaaS)-native data theft can deliver major impact without deploying encryptors.
Defenders must prioritize the common behaviors that drive ransomware impact, including abuse of external remote services, identity compromise, lateral movement over administrative protocols, and defense evasion.
Total ransomware posts on data-leak sites in Q1 2026 reached 2,638, up 22% from 2,161 in Q1 2025, reflecting the sustained pressure organizations continue to face.
But the bigger story again this quarter was instability below the top tier, across threat actors, geography, and sector. Established groups still drove large-scale disruption, yet much of the operational pressure came from newer and less established actors. As a result, actor rankings matter less than the ability to detect and disrupt the behaviors that repeatedly drive ransomware impact, including exposed VPN and RDP access; abuse of trusted admin tools; and lateral movement through RDP, Server Message Block (SMB), and Group Policy.
Ransomware-as-a-service (RaaS) groups “Akira” and “Qilin” maintained high victim counts despite quarter-over-quarter declines, while relative newcomer “The Gentlemen” surged into the top three. At the same time, two new data-leak sites, “0APT” and “ALP-001,” highly likely used questionable or fabricated “leak” claims to extort large enterprises. Meanwhile, extortion group “ShinyHunters” continued to show that even threat actors with few named victims can still drive enterprise-scale impact through identity- and software-as-a-service (SaaS)-centered intrusions.
Together, these developments show how fragmented ransomware pressure became in Q1 2026 and where organizations should focus to reduce risk in the quarters ahead.
In this report, we cover:
The Gentlemen’s sharp rise in activity, and how capable groups can break into the top tier quickly.
ShinyHunters’ identity-first intrusions, which show how low-volume activity can still create enterprise-scale impact through abuse of trusted identity workflows and SaaS platforms.
Geographic and sectoral activity, including how concentrated legal-sector targeting and continued growth in India can amplify ransomware risk through third-party and supply-chain dependencies.
Stable Leaders, A Breakout Group, and “Fake Leak” Extortion
Despite dips in overall activity this quarter, established RaaS groups Akira and Qilin continued to generate high victim volumes. At the same time, opportunistic leak-site actors added noise, coercion, and uncertainty.
The clearest example was The Gentlemen, whose activity jumped 588% quarter over quarter, from 26 posts in Q4 2025 to 179 in Q1 2026, pushing it ahead of Akira into the number two spot (see Figure 1). Defenders also faced pressure from two newly emerged, but likely fake, leak sites, 0APT and ALP-001. Because 0APT’s claims are highly likely fabricated, we exclude its 253 posts from group, sector, geography, and post-count analysis below, although the site is still included in the count of active leak sites.
The names at the top may stay familiar, but the groups generating sudden spikes in activity and incident-response noise increasingly sit further down the leaderboard. For defenders, this reinforces the need to defend against the recurrent techniques and tools that drive ransomware impact, not just track which group name is rising or falling in a given quarter.
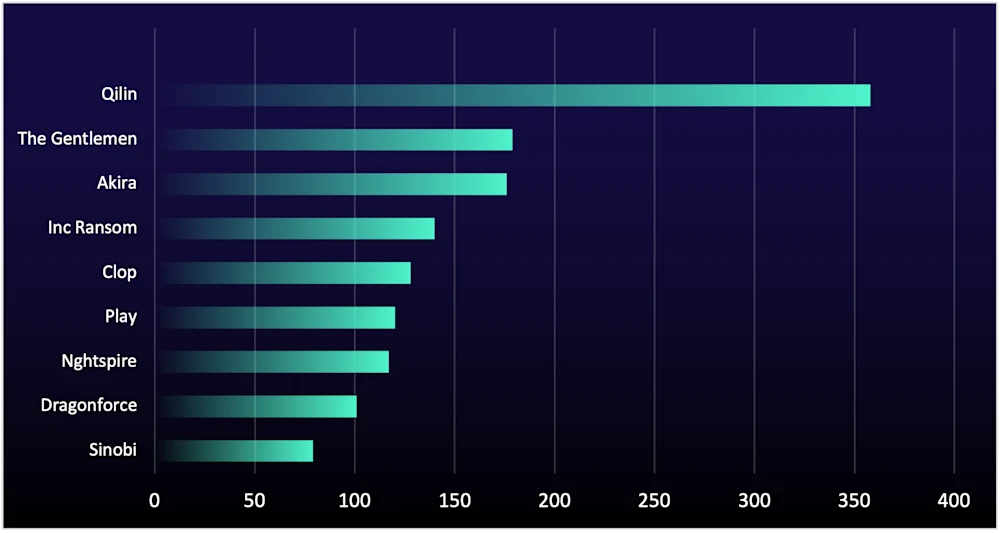
Figure 1: Number of compromised organizations listed on data-leak sites by ransomware groups, Q1 2026
The Gentlemen Activity Rises 588% to Break into Top Tier
In Q3 2025, we spotlighted The Gentlemen as a group to watch. Its Q1 2026 performance suggests that prediction has now materialized. This quarter may have been The Gentlemen’s breakout moment, but the broader takeaway is less about this one group and more about the landscape as a whole. Capable ransomware actors can surge quickly even without obvious warning signs, and next quarter the same pattern could come from a different name entirely.
What makes The Gentlemen’s activity this quarter notable is that the sharp rise doesn’t appear tied to one obvious driver like a major new campaign, a new malware release, or public recruitment push. Instead, the jump suggests the group already had the right foundations in place: effective tactics, capable operators, and repeatable operations.
Active since at least mid-2025, the group has advertised a 90/10 profit split in favor of affiliates on dark-web forums (see Figure 2), which is a more generous offer than the 80/20 model used by former dominant groups such as “RansomHub” and “ALPHV.” That commercial structure is paired with mature tradecraft and a toolkit built for speed, pointing to a structured operation rather than an opportunistic one. The group advertises that its affiliates are provided with Go-based ransomware variants for Windows, Linux, NAS, and BSD, along with a separate C-based ESXi encryptor. It also claims support for automated lateral movement, credential reuse, Group Policy-based deployment for rapid domain-wide execution, and defense evasion through disabling antivirus and firewall protections.
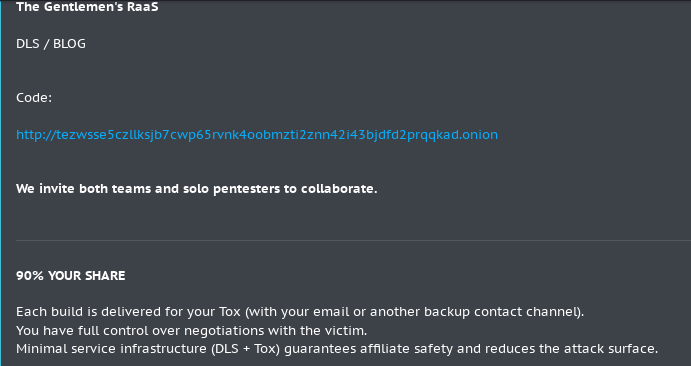
Figure 2: The Gentlemen advertising for affiliates on dark-web forum
For defenders, that reinforces a familiar but increasingly important lesson: Build preparedness around the techniques that repeatedly drive ransomware intrusions. That includes remote execution and lateral movement over administrative protocols, disabling security tools, and rapid data exfiltration. Those patterns matter more than whether this quarter’s breakout group is The Gentlemen or someone else.
Scam-Style Extortion Surfaces on New Leak Sites
The main significance of 0APT and ALP-001 is not that they’re established top-tier threats, but that even fraudulent or low-credibility leak sites can create real pressure for defenders. When an organization is named, the immediate problem isn’t attribution but rather deciding whether the claim reflects a real intrusion, a recycled dataset, or a fabricated leak. That extra validation adds time, cost, and executive pressure to an already compressed decision window.
0APT Names 253 Organizations on Its Data-Leak Site, But Questions Over Legitimacy Remain
0APT surfaced in January 2026 and closed the quarter claiming 253 victims, including large organizations across critical infrastructure, health care, finance, banking, and manufacturing. But doubts about the group’s legitimacy quickly emerged.
Several indicators undermine its credibility. In its first week, it posted a flood of alleged victims to its data-leak site, provided limited or no proof of compromise, showed no clear ties to a known ransomware variant, and reportedly required would-be affiliates to pay a 1 BTC entry deposit. Taken together, these signs suggest 0APT is highly likely fraudulent and was built to monetize attention and pressure rather than demonstrate genuine operational capability.
Even so, fake leak sites can still create real costs. If a company is named, it may still face customer questions, executive escalation, reputational concerns, and legal and communications decisions. Organizations should validate quickly by reviewing identity logs for suspicious logins and MFA changes, checking for unusual outbound transfers or SaaS export activity, and looking for signs of data staging or exfiltration before assuming the claim is real.
ALP-001: When IABs Try to Monetize More Directly
ALP-001 matters less for the volume of its claims than for the fact that it may represent an initial access broker (IAB) trying to monetize intrusions more directly, rather than selling access alone, as that offers lower returns than using the same foothold for extortion, data theft, or onward sale to ransomware affiliates.
After 0APT went quiet near quarter end, ALP-001 emerged marketing itself as a “Data Leaks / Access Market.” ReliaQuest identified that the Tox and Session IDs on ALP-001 matched those previously used by an established IAB persona on dark-web forums. This overlap suggests the same actor, or someone operating under the same persona, is attempting to expand from selling access into a broader extortion model.
However, several indicators cast doubt on ALP-001’s operational maturity. For example, some of the data that the actor has leaked was data exposed through misconfigured or publicly accessible services, including FTP servers, as well as publicly available data. The actor also appears to cycle through accounts and aliases when its credibility is challenged. Combined with public scam accusations (see Figure 3), we assess with moderate confidence that ALP-001 is a low-to-moderately sophisticated actor (or small group) trying to increase monetization through extortion branding rather than through proven compromise-and-leak capability. Organizations should therefore treat any appearance on ALP-001 as a trigger for focused validation, and not necessarily as proof of breach.
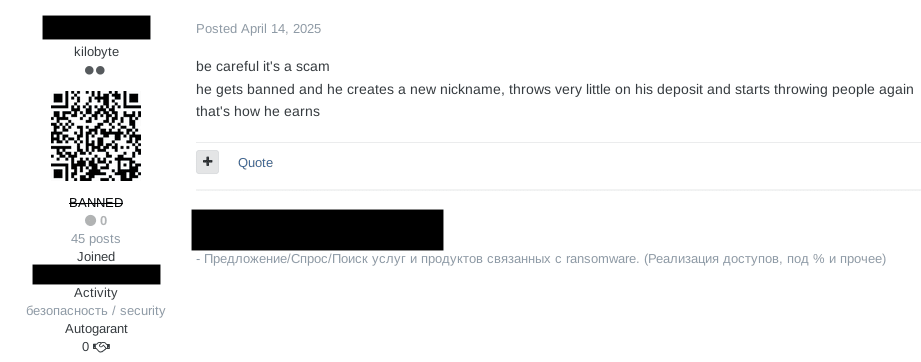
Figure 3: Dark-web forum user accusing the IAB of running scam operations
The actor has also publicly sought ransomware partners, indicating the actor may be able to obtain or broker access but lacks the in-house capability to turn that access into ransomware deployment, large-scale exfiltration, or sustained extortion operations. Security teams should therefore treat IAB exposure (e.g., stolen VPN/RDP credentials, access listings, compromised session activity) as a high-priority precursor event that warrants rapid containment, identity-focused investigation, and continuous external-risk monitoring that can surface access sales before they progress to full extortion.
ShinyHunters Delivers Outsized Impact
ShinyHunters listed only 34 organizations this quarter, but it still delivered disproportionate impact by operating in the gaps between identity, SaaS, and mobile—areas where many enterprises still have limited defense visibility. And one compromised session can provide broad access to multiple business-critical platforms and enable large-scale data theft without deploying malware.
While better known as a data-theft and extortion actor than a traditional ransomware group, we’re including ShinyHunters in this report because it uses the same core leverage model: Steal high-value data and monetize access through extortion.
Its first access path is via calling employees on personal mobile phones, impersonating IT help-desk staff with spoofed caller IDs, and directing targets to highly customized phishing domains that mimic Okta login and support workflows (e.g., [company]sso[.]com, [company].passkeysetup[.]com). These themes work because they imitate the systems users already trust for authentication, password resets, and MFA setup, making them more likely to seem legitimate in the moment. By targeting personal devices over cellular networks, the group can also bypass corporate web proxies and domain blocklists.
ReliaQuest continues to track phishing domains likely tied to ShinyHunters that impersonate trusted identity brands. To date, it has identified around 500 domains tied to this activity.
Once credentials are captured through adversary-in-the-middle (AiTM) infrastructure, attackers can quickly reset passwords, enroll new MFA devices, and establish persistent access. They then use single sign-on (SSO) access to move into SaaS environments—particularly Salesforce and SharePoint—where they can exfiltrate data via legitimate APIs and bulk downloads.
Its second access path doesn’t require user interaction. Between late 2025 and March 2026, the group exploited Salesforce Experience Cloud misconfigurations using a modified version of the open-source AuraInspector tool, claiming 300–400 breaches.
These two access paths are operationally different, but they lead to the same extortion outcome. One relies on identity compromise through vishing or phishing; and the other exposed SaaS configurations. Together, they show a repeatable, high-efficiency intrusion model built around identity compromise, misconfiguration abuse, and rapid access to large volumes of enterprise data.
For defenders, that means social engineering awareness alone is not enough. Organizations need parallel coverage for identity abuse, suspicious SaaS activity, and exposed public-facing SaaS configurations.
Step Up Your Defenses Against ShinyHunters
Set conditional access policies to only allow access to sensitive SaaS applications like Salesforce and Sharepoint via a managed, compliant device
Extend security awareness beyond email to include vishing, particularly help-desk impersonation and unsolicited MFA enrollment requests on personal devices.
Alert on rapid password resets, new MFA device enrollments, and SSO logins from anomalous locations for the earliest indicators of compromise.
Enable and actively monitor SaaS application logging, especially for high-volume API access, bulk downloads, mass exports, and unusual administrative activity in platforms such as Salesforce and SharePoint.
The Current Landscape: New Groups and Top Trends
Data-Leak Sites Reach a New High of 91 After Q4 2025 Slump
The clearest signal from Q1 2026 is that the leak-site environment remains highly fragmented. The number of active data-leak sites rose to a record high of 91 (see Figure 4), beating its previous peak of 84 in Q3 2025 and rebounding from 77 in Q4 2025.
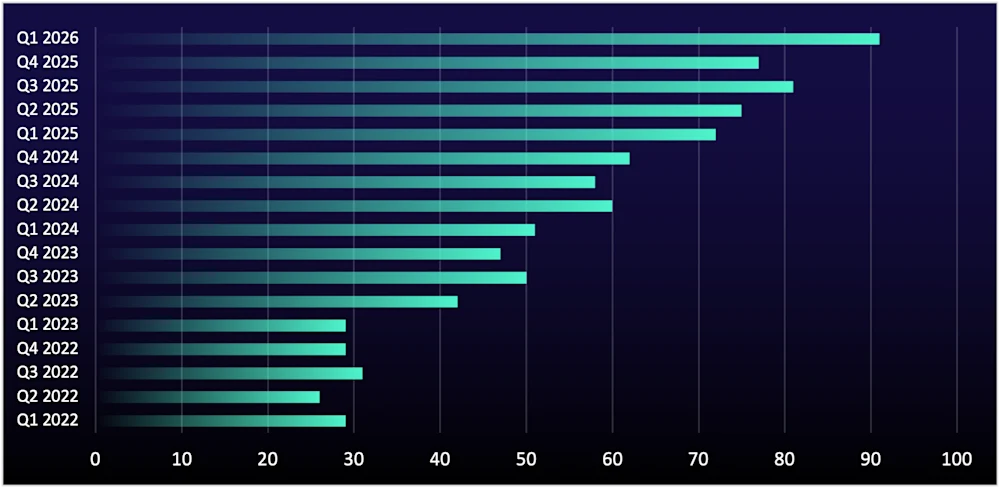
Figure 4: Active data-leak sites from Q1 2022–Q1 2026
More active leak sites mean more potential sources of extortion pressure, more targeting variability, and a greater chance of exposure—either directly or through third parties. That increases the burden on incident response, legal, and communications teams, especially when some sites may be exaggerating or fabricating victim claims. The result is a noisier environment in which organizations need to quickly distinguish between credible compromise and pressure tactics.
That challenge exists alongside the speed of real ransomware intrusions. Groups like Akira and Qilin are already compressing response timelines, with Akira even initiating lateral movement in as little as six minutes. In other words, defenders now face even more pressure to move fast.
Quarter-to-quarter swings in leak-site activity reflect how financially motivated actors adapt to market conditions. When dominant groups decline, smaller groups launch independent operations to fill the gap. Conversely, when dominant groups emerge, operators may gravitate toward them because they offer stronger profit potential, more credible extortion pressure, and more mature infrastructure for negotiations and leaks. And this ebb and flow is likely to continue.
Inc Ransom Targets Legal Services While PSTS Stays Top
Professional, scientific, and technical services (PSTS) remained the most-targeted sector for the fourth consecutive quarter (see Figure 5), with posts rising 14% quarter over quarter, from 736 in Q4 2025 to 840 in Q1 2026. The significance extends beyond the sector itself, because even organizations not directly named may still be exposed through their reliance on PSTS providers such as law firms, consultants, accountants, and engineering partners. When one of these firms is compromised, the fallout can extend to client data, shared systems, ongoing projects, and trusted business relationships.
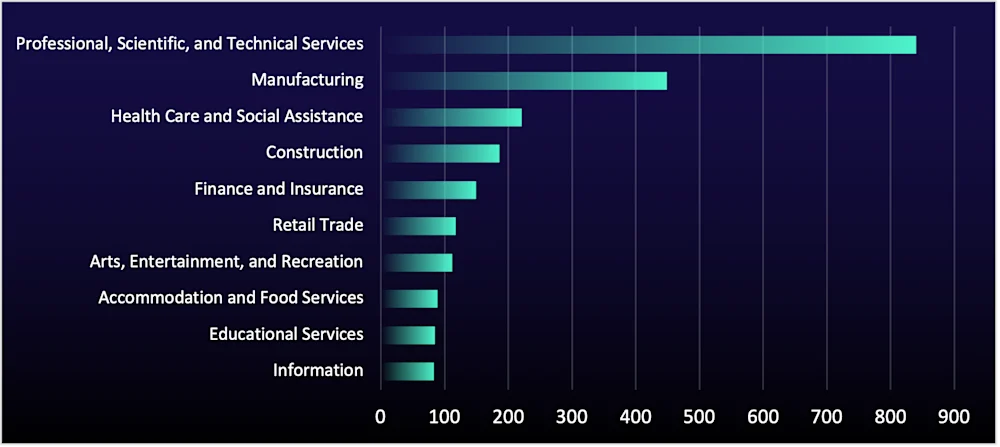
Figure 5: Number of organizations listed on data-leak sites, by sector, in Q1 2025
A key driver this quarter was the cluster targeting of 16 law firms and legal services organizations by “Inc Ransom” within a short window. This likely reflects either deliberate legal-sector targeting or, more likely, access to a shared third-party platform. If a common provider was compromised, one intrusion could expose multiple firms and their clients, increasing the scale and downstream impact of extortion. Several entries showed recurring cloud-storage-style directory structures, suggesting the affected data may have been stored or exchanged through cloud-based repositories commonly used in legal workflows. While unconfirmed, this strengthens the possibility of a shared cloud-storage access path.
Law firms hold especially high-leverage data, including attorney-client privileged communications, financial records, tax data, and sensitive case materials. Exposure of that information can create legal, regulatory, and contractual consequences that extend beyond the firm to its clients and partners. Organizations should audit third-party legal technology vendors, document management platforms, and cloud storage providers for indicators of compromise, and check whether any shared providers have recently disclosed a breach.
US Remains Top Target While Attacks on India Raise Supply-Chain Risk
Geographic trends stayed consistent at the top this quarter but volatile below it. India rose 33% in Q1 2026 after significant growth in late 2025. Increased targeting in India has global downstream implications. Organizations with manufacturing operations, supply-chain dependencies, subsidiaries, or outsourced IT relationships in India face elevated risk, because a ransomware event at an India-based entity can cascade into operational disruption across global operations. Security teams should prioritize segmentation controls (especially IT/operational technology [OT] boundaries) and contractual security requirements for third parties.
The US was again the most targeted country (see Figure 6), increasing from 1,359 in Q4 2025 to 1,473 in Q1 2026. It likely remains attractive because of high payouts, a large victim pool, and the prevalence of cyber insurance that often covers ransomware payments.
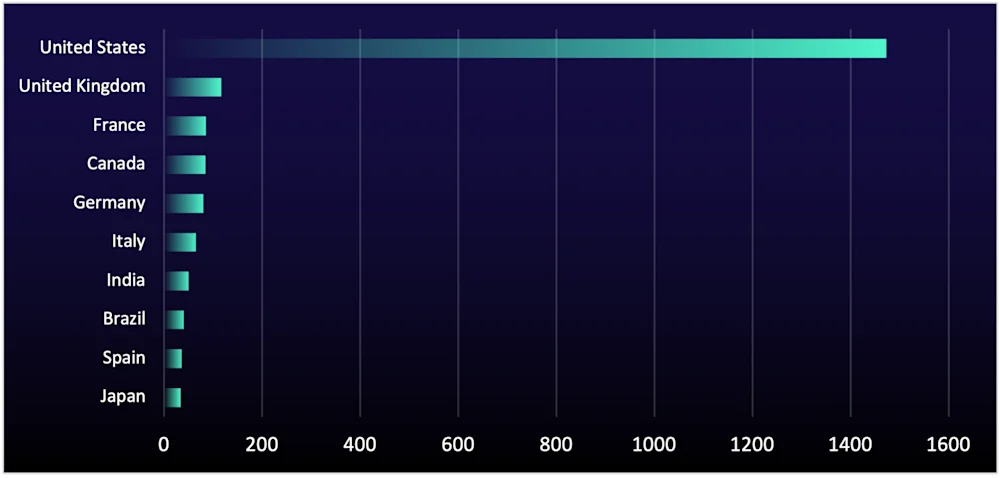
Figure 6: Number of organizations listed on data-leak sites by country, Q1 2026
The quarter-to-quarter spikes in smaller markets often reflect one-off campaign activity rather than sustained geographic focus or durable shifts. India was the most notable mover this quarter, but as with Thailand and the UAE in recent quarters, those increases typically don’t persist.
Step Up Your Defenses Against Ransomware
ReliaQuest’s Approach
ReliaQuest GreyMatter helps organizations reduce ransomware impact by improving detection speed, automating containment, and expanding visibility into both internal exposures and external risk signals, which is critical in a quarter defined by affiliate scale and scam leak noise.
GreyMatter Transit: Detect threats as data moves between source and storage, helping close the gap when groups like Akira move laterally in minutes.
GreyMatter Discover: Automate asset discovery and exposure visibility to identify unmanaged assets, coverage gaps, and misconfigurations that RaaS affiliates routinely exploit.
Digital Risk Protection (DRP): Counter record leak-site activity and scam leak noise by monitoring the open, deep, and dark web and helping validate whether exposure claims are credible.
Pair ReliaQuest’s tailored detection rules with the following GreyMatter Automated Response Playbooks to contain ransomware threats in as little as five minutes:
Isolate Host: Infected hosts can provide initial access to ransomware affiliates, restrict their access to critical resources by isolating the host before damage can be done.
Disable User: Ransomware groups like Akira and Qilin often gain access by simply authenticating to RDP or VPNs, revoke their access by disabling compromised accounts.
Initiate Host Scan: When ransomware activity is suspected, automatically trigger a scan of the affected endpoint to quickly confirm malicious artifacts and scope compromise so teams can contain the threat before it spreads or data is exfiltrated.
Your Action Plan
Ransomware remains one of the most disruptive threats organizations face. Follow these steps to put your organization in the best position to catch the ransomware threats mentioned in this report early, before they cause business disruption.
Restrict RDP and Remote Access: Use device-based certificates to block attackers using stolen VPN credentials from IABs. Limit RDP access to essential accounts and hosts, enforce network segmentation to restrict access to authorized sources, and ensure users fully log out of sessions when not in use. Ransomware affiliates often gain access through exposed RDP and VPN portals, making stronger authentication measures critical to preventing intrusions.
Review Shared Repositories and Third Parties: Audit cloud storage platforms, document management systems, and legal technology vendors for suspicious access, exposed data, and recent breach disclosures. Inc Ransom’s legal-sector clustering suggests a single compromised provider could have downstream impact across multiple organizations.
Harden identity against vishing and AiTM: Train employees to recognize and report vishing and phishing attempts, establish clear protocols for verifying IT support requests, and implement phishing-resistant MFA such as FIDO2 hardware keys to reduce the effectiveness of AiTM credential harvesting.
Review Third-Party and India-Linked Exposure: Audit legal technology vendors, document platforms, and cloud storage providers for signs of compromise, and reassess segmentation, incident response coverage, and contractual controls for subsidiaries, suppliers, and outsourced IT relationships in India.
Key Takeaways
Q1 2026 reinforced that ransomware is no longer a matter of tracking the biggest group names but a broader operational problem shaped by affiliate-driven scale, rapid actor turnover, and a leak-site ecosystem that’s getting larger and noisier. And that volatility is likely to persist into next quarter and beyond, producing uneven shifts in victimology across sectors and geographies while increasing the number of situations where security teams must validate extortion claims under intense time and executive pressure.
At the same time, ShinyHunters reinforced a direction other financially motivated actors may follow, i.e., identity-first intrusion and SaaS-native data theft that can deliver high-impact extortion without deploying traditional encryptors. Because this playbook is efficient, repeatable, and often falls outside endpoint-centric visibility, it will likely expand to other actors looking for faster paths to leverage and payout.
In this environment, the strongest defensive advantage comes from moving beyond reactive, actor-led response toward a more proactive and predictive posture. That means focusing detections and response on specific behaviors (like abuse of VPN and RDP access, identity compromise, lateral movement over administrative protocols, defense evasion, and rapid data exfiltration from SaaS and file stores), while using automation and AI-led security operations to validate exposure early, surface external risk signals, and contain threats faster. Attribution still adds context, but resilience comes from identifying and disrupting the intrusion chain before it becomes business disruption.