The Self-Replicating Worm: Shai-Hulud’s
Supply-Chain Carnage
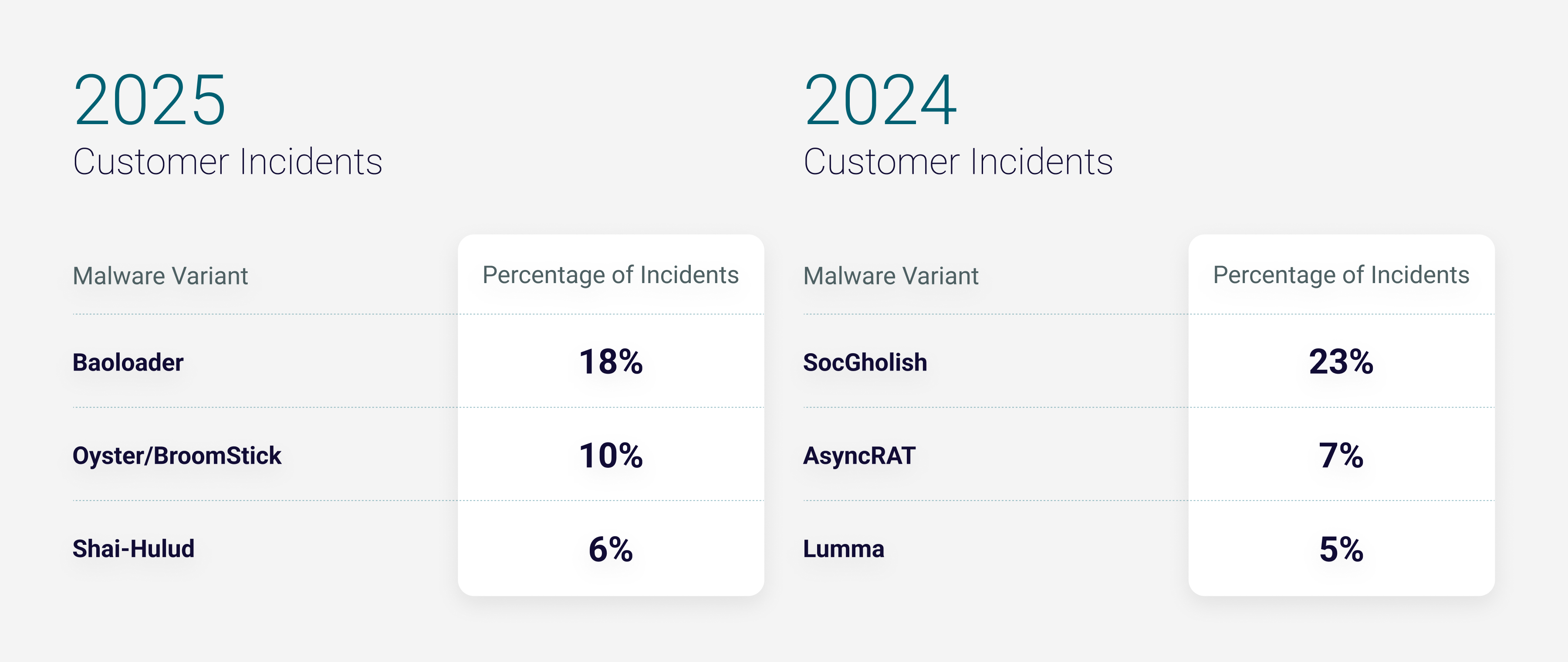
First observed in September 2025, Shai-Hulud quickly rose to become the 3rd most prevalent
malware
family, showing how attackers can weaponize trusted maintainer accounts and routine software
updates
to achieve outsized impact.
Unlike traditional malware that targets a single endpoint, Shai-Hulud exploits the
interconnected
nature of modern software development, meaning a single compromised package can attempt to
spread
into thousands of dependent projects.
In the cases we tracked involving Shai-Hulud, threat actors used phishing campaigns disguised as
official npm security alerts to steal maintainer credentials. Once inside those accounts, they
poisoned trusted packages. Developers became infected through normal actions like running
routine
updates or executing standard CI/CD pipelines, without realizing libraries they’d used for
months
had been silently tampered with.
Invisible Execution and Exponential Spread Through Borrowed Trust
Shai-Hulud’s effectiveness comes down to when it executes and how it spreads.
In one observed incident, it ran early in the install process, before security checks, reviews,
or
CI guardrails could catch it. To developers, everything looked normal: The package installed
successfully while Shai-Hulud quietly launched its payload in the background.
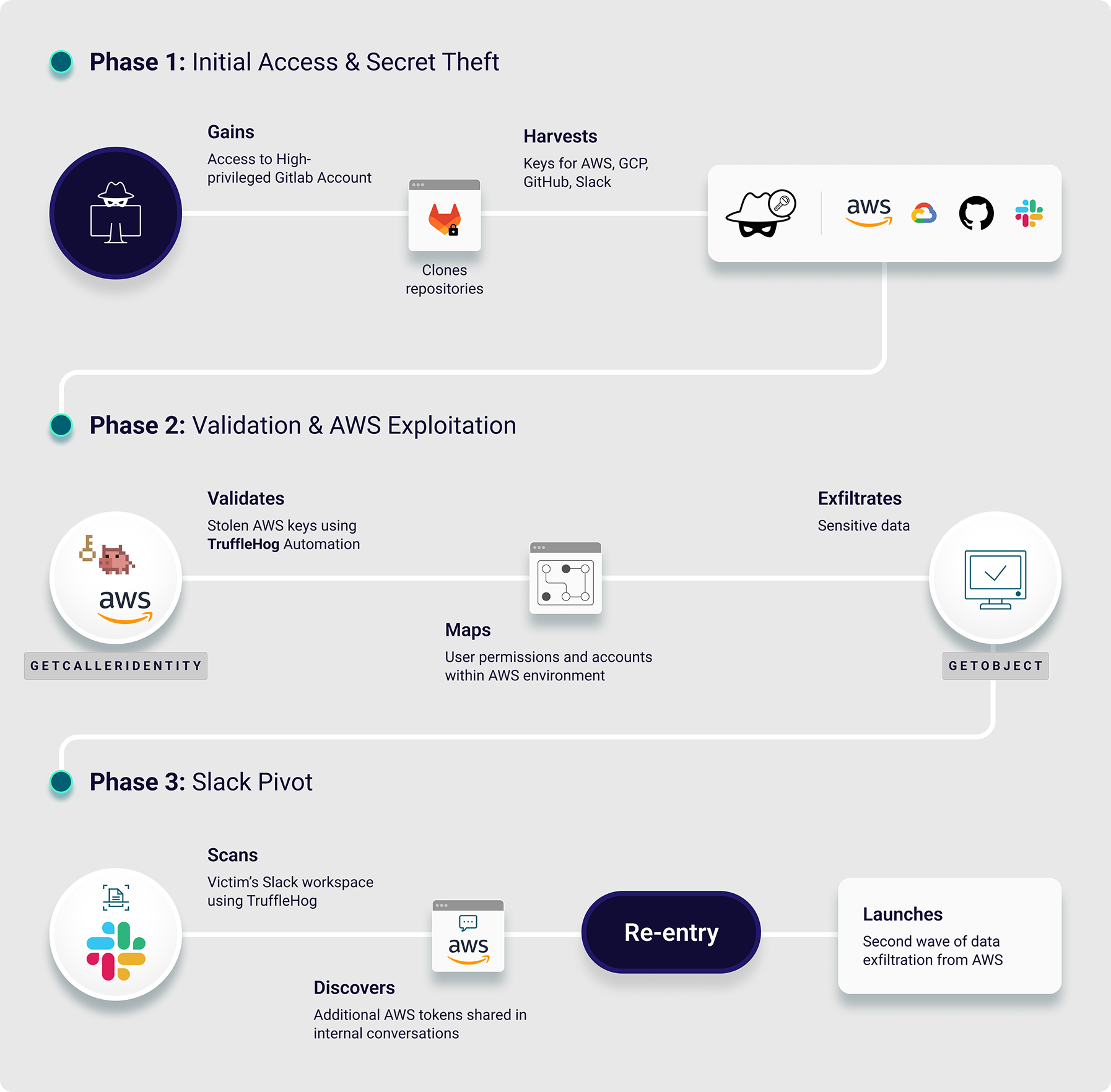
Once active, it went after high-impact credentials: npm tokens, GitHub access tokens, SSH keys,
and
cloud credentials (AWS, Azure, and Google Cloud). It also leveraged TruffleHog, a legitimate
secrets-scanning tool, to harvest sensitive information from local files and environments.
Stolen
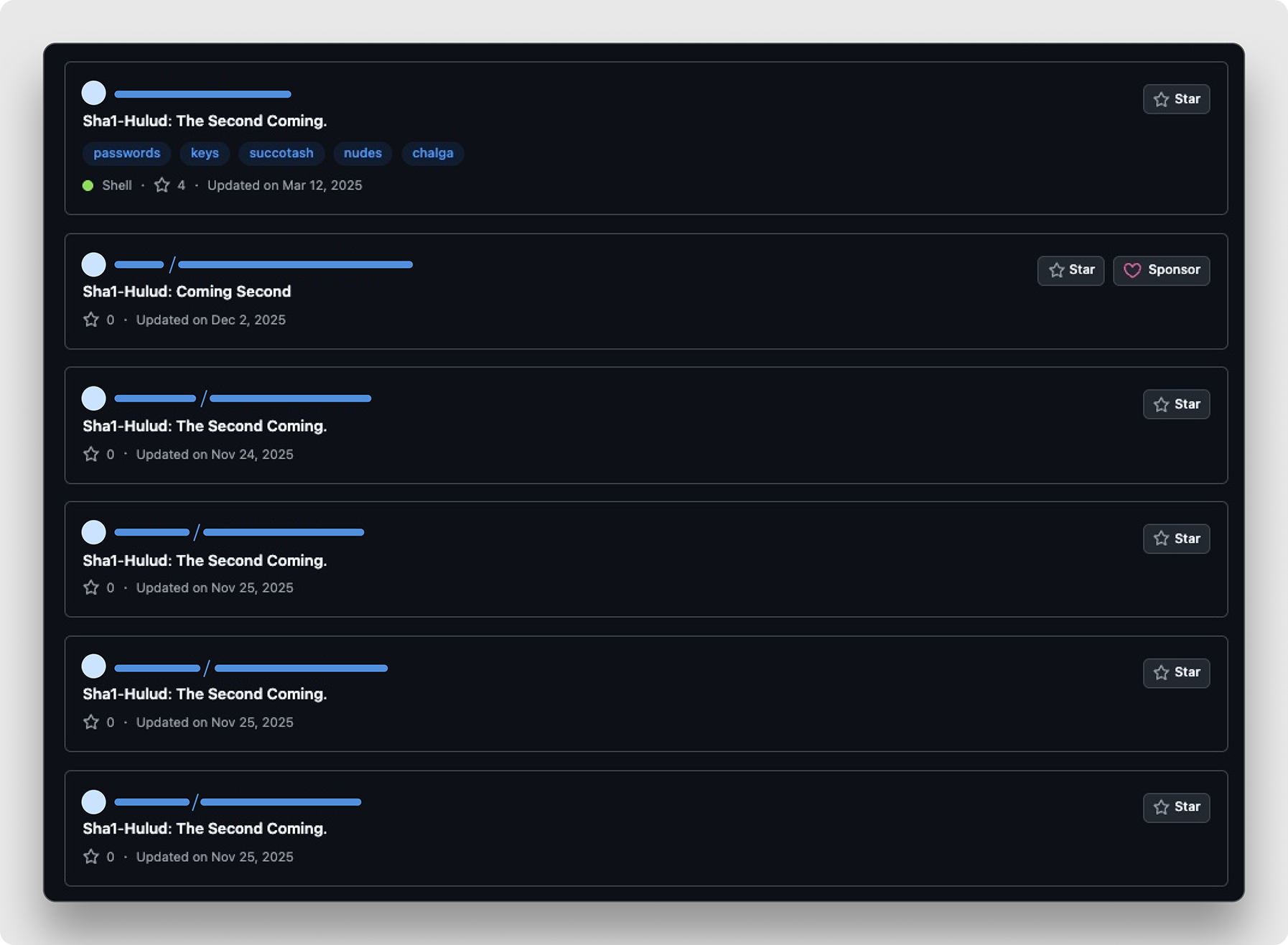
data was pushed to newly created public GitHub repositories, effectively publishing secrets in
plain
sight.
A “2.0” wave just months later added a destructive twist: If credential theft failed, the
malware
attempted to wipe the victim's home directory, turning theft into sabotage.
The business risk of Shai-Hulud is cascading. The cloud credentials, API keys, and GitHub tokens
that Shai-Hulud steals can directly unlock production environments, CI/CD pipelines, and
proprietary
source code. With this access, the attackers can move on to lateral movement, data exfiltration,
and
intellectual property theft, with potential follow-on ransomware deployment across the entire
software development infrastructure.