A New Era for Security Detection
As a security leader, your mission is to enable the business to move fast while managing risk. Yet the standard playbook for detection—the cornerstone of any security program—is slowing you down and introducing risk.
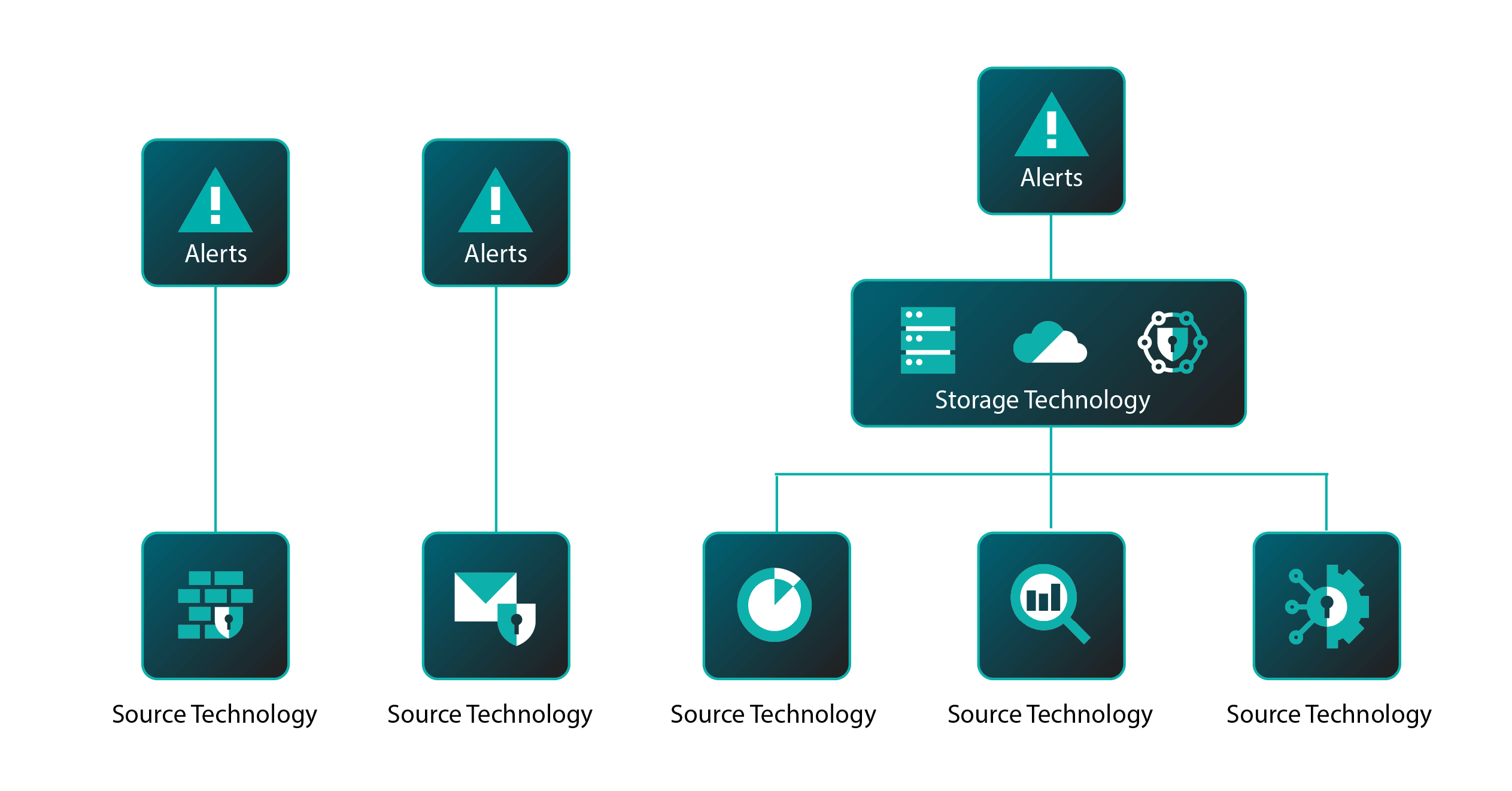
Imagine your firewall detects suspicious traffic, but the data has to flow to your SIEM, get ingested, and trigger correlation before an alert fires. Valuable hours pass before your team sees it. Meanwhile, you’re paying to store every byte of that data, including logs that never trigger a detection. If you try to cut costs by forwarding data selectively, you sacrifice comprehensive visibility—you're forced to choose.
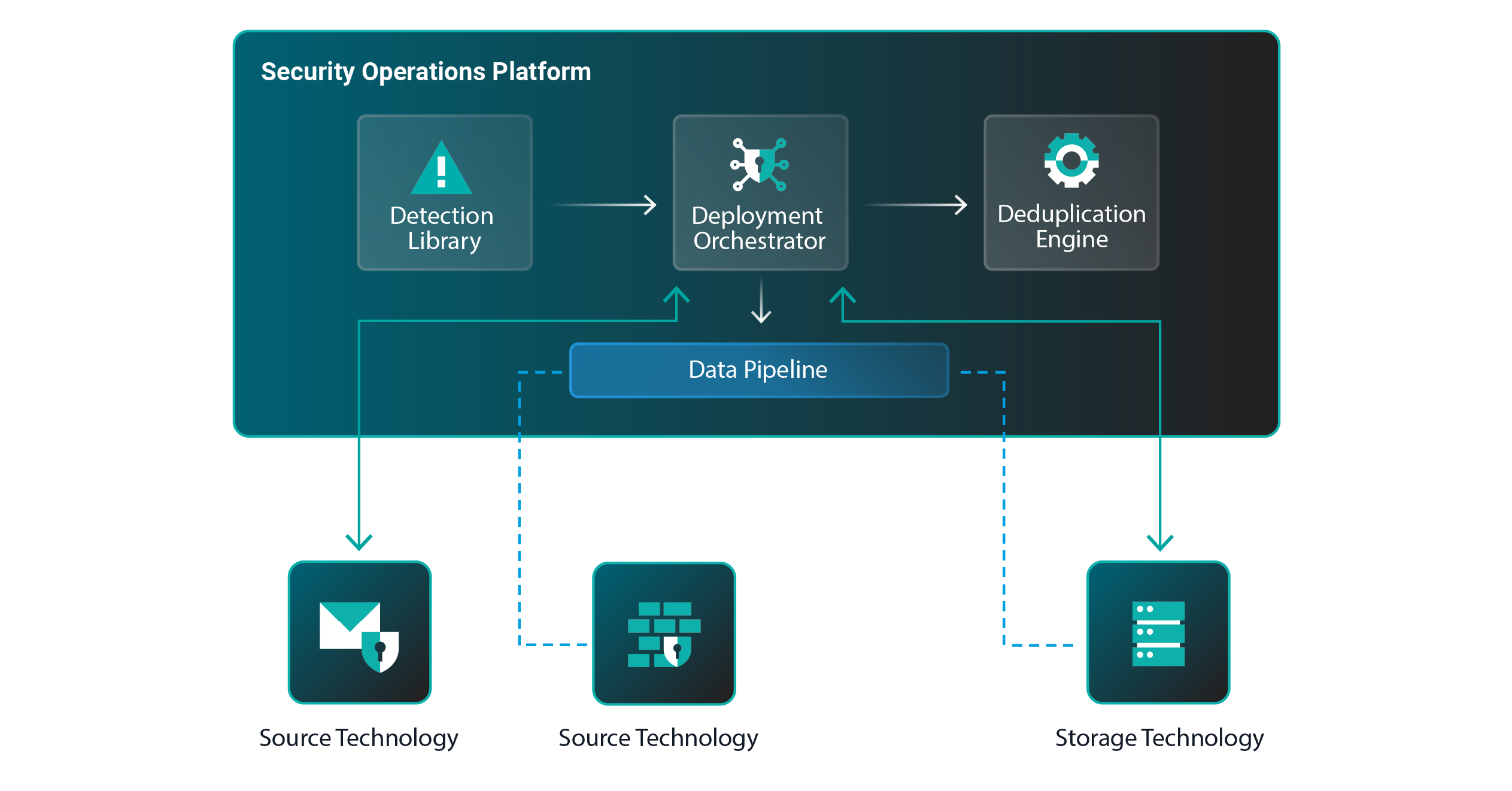
Leaders can simultaneously achieve speed, cost, and visibility by adopting a new strategic mindset: detection optionality. This approach decouples detection from data storage and empowers you to choose the most effective and efficient way to detect threats.